
Google’s Threat Intelligence Group reported 90 zero‑day vulnerabilities actively exploited in the wild across 2025. That total sits above 2024’s 78 but below the record 100 observed in 2023. Beyond the raw count, the GTIG data reveals a notable shift in where and how these flaws were used, who is using them, and which technical weaknesses continue to drive high‑impact attacks.
The raw picture
GTIG split the 90 exploited zero‑days roughly evenly between end‑user platforms and enterprise products: 47 targeted end‑user systems and 43 targeted enterprise technologies. Memory‑safety issues accounted for roughly a third of exploited vulnerabilities, and the types of flaws included remote code execution, privilege escalation, injection/deserialization flaws, authorization bypasses, and classic memory corruption (use‑after‑free) bugs.
Which platforms and vendors were hit
Operating systems were the most exploited category: 24 zero‑days affected desktop OSs and 15 affected mobile platforms. Browser zero‑day exploitation dropped to eight instances in 2025, a decline that GTIG attributes partly to stronger browser hardening and possibly to better concealment by attackers. Among vendors, Microsoft topped the list with 25 zero‑days attributed, followed by Google with 11 and Apple with eight. Cisco and Fortinet each had four zero‑days tracked, while Ivanti and VMware had three apiece.
Shifts in who is wielding zero‑days
For the first time in GTIG’s tracking, commercial surveillance vendors (CSVs) were the largest users of undocumented flaws, surpassing traditional state‑sponsored espionage groups. State‑linked actors—particularly China‑affiliated groups—remained active and are noted for targeting edge devices, security appliances, and networking equipment to secure long‑term access. Financially motivated actors, including ransomware and extortion groups, exploited nine zero‑day flaws in 2025, underscoring that advanced exploits are no longer restricted to nation‑state arsenals.
Attack patterns and strategic trends
Enterprise infrastructure and edge devices were prominent targets because they offer privileged network access and often lack comprehensive EDR coverage. Security appliances, VPNs, routers, and virtualization platforms were frequently exploited for initial access and persistence. There is evidence of increased chaining of multiple bugs—especially on mobile platforms—to escalate privileges and achieve deeper control. GTIG also highlights campaigns that prioritize theft of source code and intellectual property, which in turn accelerates discovery of future zero‑days. The report notes that AI and automation tools are expected to increase the pace of vulnerability discovery and exploit development, likely keeping zero‑day activity elevated.
What the facts imply for defenders
The telemetry points to concrete priorities: edge and appliance software emerge as high‑risk categories, memory‑safety defects remain a major contributor to exploited bugs, and the exploit market now includes well‑funded commercial actors. Practical defensive measures flow directly from these observations: hardening and monitoring of edge devices and network appliances; maintaining an accurate asset inventory and Software Bill of Materials to map components quickly when a new zero‑day appears; and accelerating detection and remediation processes. GTIG’s advice emphasizes reducing attack surfaces and privilege exposure, continuous behavioral monitoring for anomalous activity, and rapid patching and incident response when exploitation is detected.
A closing view
The 2025 data show not just a number but a changing ecosystem: new types of buyers and users, shifting target priorities, and accelerating tooling that shortens the time from discovery to exploitation. The landscape is dynamic, and the concrete, observable trends in GTIG’s report—where zero‑days occurred, which vendors were hit, which actors used them, and which technical classes of bugs were most exploited—should shape operational priorities for security teams aiming to reduce risk and shorten their reaction window.
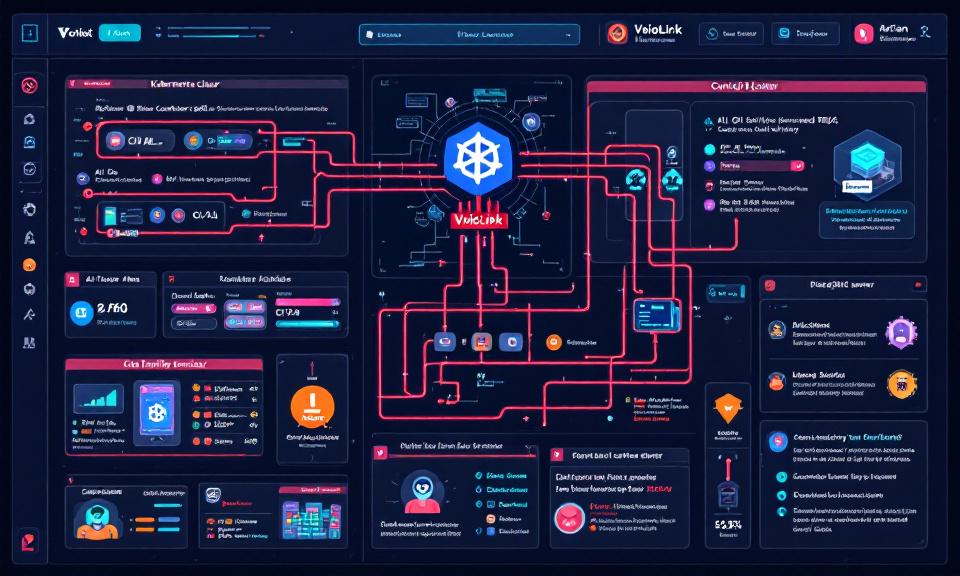
VoidLink Malware Framework: Key Points on How It Targets Kubernetes and AI Workloads
Title: VoidLink Malware Framework: Key Points on How It Targets Kubernetes and…
When Local Trust Breaks: The OpenClaw 0-Click Vulnerability and What Developers Must Do Now
The speed at which developer-facing AI agents have been adopted is staggering…

When a Jailbreak Became a Campaign: How Claude AI Was Abused to Build Exploits and Steal Data
In late 2025 a persistent attacker turned a conversational AI into a…

Citrix Warns: Patch NetScaler ADC and Gateway Flaws Immediately
Citrix has released urgent security updates for NetScaler ADC and NetScaler Gateway…