Google has finalized its acquisition of Wiz, the Israeli cloud and AI security company, in an all-cash transaction valued at $32 billion. The deal, announced as closed in March 2026, is the largest acquisition in Google’s history and represents a major move by Google Cloud to deepen its capabilities in cloud-native and AI security. Deal overview The acquisition brings the
Category: Cloud-Computing
EC2, S3, Lambda, RDS, DynamoDB, VPC, CloudFront, Route 53, IAM, CloudWatch, EKS, VMs, Blob Storage, Azure Functions, Azure SQL, Cosmos DB, VNet, Azure AD, Azure Monitor, AKS, Compute Engine, Cloud Storage, Cloud Functions, Cloud SQL, BigQuery, GKE, Pub/Sub, Cloud Run, App Engine.
China’s OpenClaw Gold Rush: How a Viral AI Agent Spawned a New Service Economy
China has seen a rapid, real-world surge of interest in OpenClaw — an open-source AI agent that can run autonomously on personal devices — and that surge has produced a small but booming service economy of installers, preconfigured devices, and paid support. This post summarizes reported facts about how OpenClaw spread, who is profiting, what services are being offered, and
Introducing the Azure Skills Plugin: Practical Azure Workflows for Coding Agents
The Azure Skills Plugin brings curated Azure expertise and an execution layer together so coding agents can do more than offer generic guidance. Rather than just suggesting commands or linking to documentation, the plugin packages decision logic (skills) and structured tools (MCP servers) so agents can reason about workflows and, when appropriate, run actions against real Azure resources. What the
Zero-Day on the Market: $220K Exploit Targets Windows Remote Desktop Services (CVE-2026-21533)
Remote Desktop Services (RDS) has come under renewed scrutiny after reports that a working exploit for CVE-2026-21533 — an elevation-of-privilege vulnerability in Windows Remote Desktop Services — was listed for sale on a dark web forum for $220,000. The listing and surrounding reporting are factual and straightforward: a recently created account advertised a claimed zero-day exploit, observers recorded the posting,
From Tunnel to Cloud: The 2026 Strategy Guide to Self‑Hosting vs Third‑Party VPN
In 2026 the boundary between “VPN” and “personal cloud” is fuzzier than ever. A third‑party VPN still sells one‑click privacy and wide geo-hopping, but for many users that convenience now trades away transparency, extensibility, and long‑term value. Renting a small VPS and running WireGuard, AdGuard Home, Vaultwarden, and automation tools like n8n converts a disposable privacy tool into a persistent
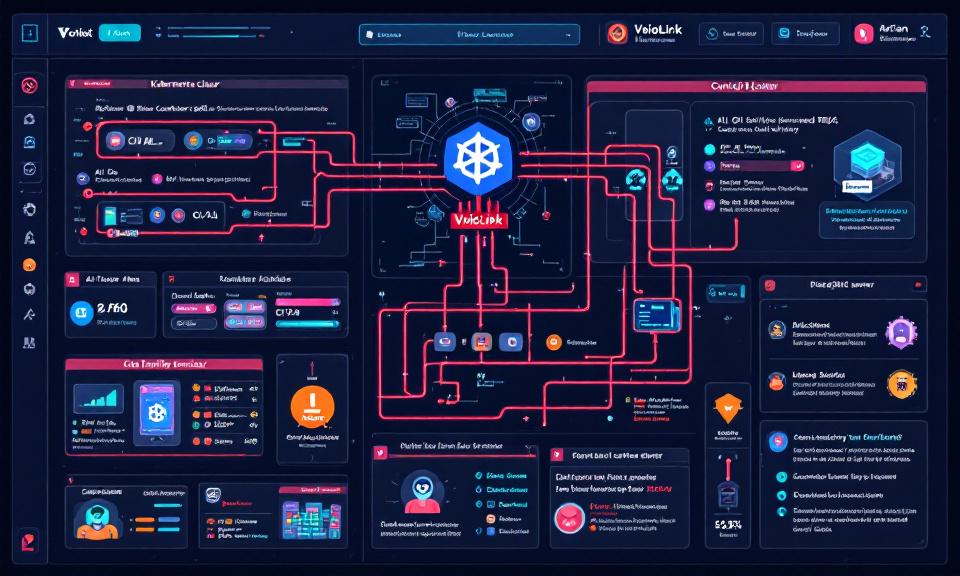
VoidLink Malware Framework: Key Points on How It Targets Kubernetes and AI Workloads
Title: VoidLink Malware Framework: Key Points on How It Targets Kubernetes and AI Workloads Overview VoidLink is a modular malware framework observed targeting cloud-native environments, with emphasis on Kubernetes clusters and AI infrastructure. Goal: persistence, lateral movement, data exfiltration, and abuse of compute (e.g., model theft, crypto-mining, or training/serving misuse). Modularity enables plugins for container escape, kubeconfig harvesting, and targeted