
Microsoft has issued an emergency security update to address a newly disclosed vulnerability in the .NET ecosystem that can be triggered remotely and results in denial-of-service (DoS) conditions. The flaw, tracked as CVE-2026-26127, affects multiple .NET runtime and package versions across Windows, macOS, and Linux. Administrators and developers should prioritize applying the available patches to prevent service disruption.
What the vulnerability is
CVE-2026-26127 is an out-of-bounds read vulnerability (CWE-125). An out-of-bounds read occurs when code reads memory outside an allocated buffer, which can lead to crashes or undefined behavior. In this case, specially crafted network requests against a vulnerable .NET application can provoke such a memory read, causing the application to terminate and denying service to legitimate users. The vulnerability can be exploited without authentication or elevated privileges.
Severity and exploitability
Microsoft has assigned a CVSS score of 7.5 to this issue and classified it as Important. While the vulnerability’s exploitability assessment is currently listed as “Unlikely,” the underlying conditions are such that an attacker with network access and the ability to send crafted requests could trigger a DoS. Public disclosure of the vulnerability’s details increases the theoretical risk that exploit code could be developed in the future.
Affected software
The vulnerability impacts core .NET installations and a memory-related NuGet package:
- .NET 9.0 on Windows, macOS, and Linux
- .NET 10.0 on Windows, macOS, and Linux
- Microsoft.Bcl.Memory package versions corresponding to 9.0 and 10.0
Mitigations and patches
Microsoft has released security updates to remediate the flaw. The recommended actions are:
- Update .NET 9.0 environments to the patched build 9.0.14 (all supported operating systems).
- Update .NET 10.0 environments to the patched build 10.0.4 (all supported operating systems).
- If using Microsoft.Bcl.Memory, update the NuGet package to the patched versions (9.0.14 or 10.0.4 as appropriate).
Operational recommendations
- Apply the official patches from Microsoft as soon as possible to remove the vulnerability.
- Monitor application and system logs for unexpected crashes or anomalous network requests that could indicate attempted exploitation.
- Validate CI/CD and dependency management pipelines to ensure NuGet package updates are applied and deployed in a timely manner.
- For externally facing services written in .NET, consider additional network-layer protections (rate limiting, request validation, WAF rules) while applying fixes.
- Maintain a tested rollback plan and backup procedures before and after applying updates in production environments.
Current threat landscape
At the time of disclosure there is no confirmed evidence of active exploitation in the wild and no indication of mature exploit code circulating publicly. However, a researcher has disclosed the vulnerability details, which could accelerate development of working exploits. Given that the flaw can be triggered remotely without interaction, timely patching remains the safest course.
Conclusion
CVE-2026-26127 is a remote, unauthenticated out-of-bounds read in .NET that can cause service outages. Microsoft’s patches for .NET 9.0 (9.0.14), .NET 10.0 (10.0.4), and the Microsoft.Bcl.Memory package address the issue across Windows, macOS, and Linux. Organizations should patch affected systems immediately, monitor for anomalous behavior, and ensure dependency updates are incorporated into deployment workflows.

Hackers Leverage Microsoft Teams to Breach Organizations: Inside UNC6692’s SNOW Campaign
In late 2025 and into early 2026, a sophisticated intrusion campaign used…
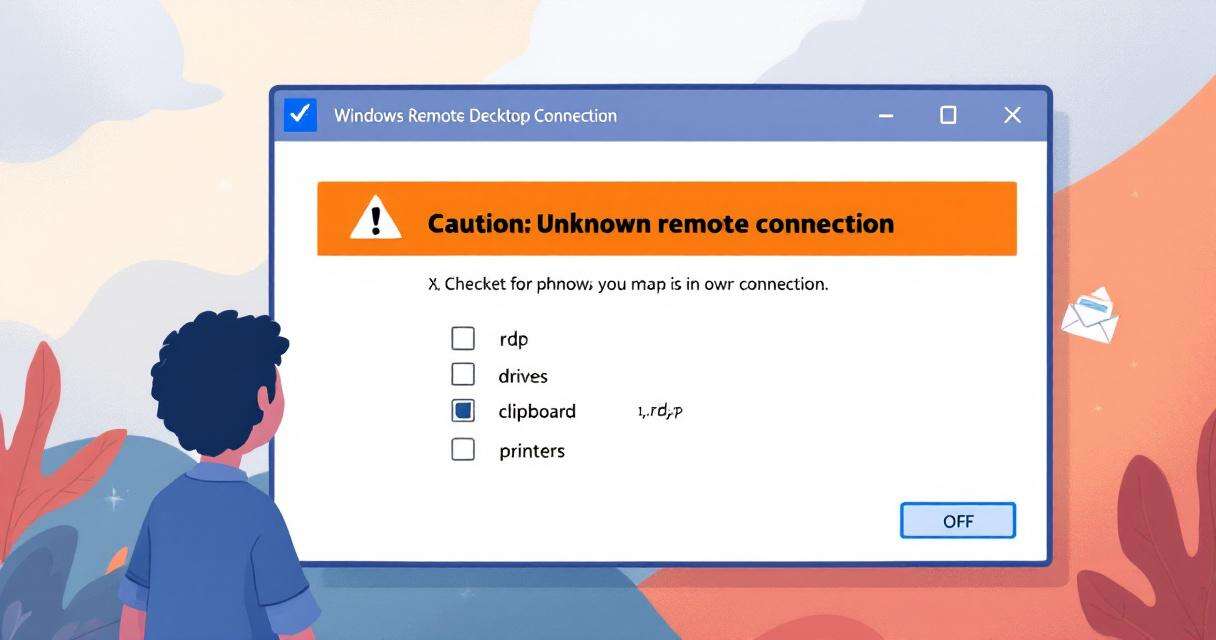
New RDP Alert After April 2026 Security Update Warns of Unknown Connections
Microsoft’s April 2026 Patch Tuesday introduced a small-looking but important change to…

Recently Leaked Windows Zero-Days Now Being Actively Exploited: What You Need to Know
Threat actors have begun abusing three recently disclosed Windows vulnerabilities to escalate…

RedSun: New Microsoft Defender Zero-Day Lets Unprivileged Users Gain SYSTEM Access
A freshly disclosed zero-day vulnerability in Microsoft Defender, dubbed "RedSun," has raised…