
A freshly disclosed zero-day vulnerability in Microsoft Defender, dubbed “RedSun,” has raised alarms across enterprise security teams: an unprivileged user can escalate to full SYSTEM-level access on fully patched Windows systems. The flaw was detailed publicly in April 2026 by a researcher known as “Chaotic Eclipse” (also referenced as Nightmare‑Eclipse on GitHub). Independent verification from vulnerability analyst Will Dormann confirms the exploit works reliably on current Windows releases, and as of this writing no official patch has been issued.
What RedSun is and why it matters
RedSun exploits a logic flaw in Defender’s cloud file handling mechanism. Instead of simply quarantining or removing files flagged with a cloud tag, Defender’s cloud subsystem can rewrite the file back to its original filesystem location. That benign-seeming behavior becomes dangerous when an attacker manipulates the write targets: by combining Windows Cloud Files API operations with opportunistic locks (oplocks) and NTFS reparse points, Defender can be tricked into overwriting critical system binaries with attacker-controlled data — and because Defender performs the write under elevated privileges, the attacker gains SYSTEM-level code execution. In short, a user without administrative rights can coerce a trusted system component into performing a privileged write on their behalf.
How the exploit chain works
- An attacker writes a benign-looking file (the proof‑of‑concept used an EICAR test file) via the Windows Cloud Files API (cldapi.dll).
- An opportunistic lock is used to pause Defender’s restoration operation at a precise moment.
- NTFS directory junctions or reparse points redirect the resumed write to a protected location such as C:WindowsSystem32.
- Defender follows the redirected path and overwrites a system binary (examples cited include TieringEngineService.exe) with content the attacker controls.
- The attacker then launches or otherwise triggers the overwritten binary, achieving SYSTEM-level execution.
Affected platforms and scope
The vulnerability affects any Windows machine running Defender with the cldapi.dll component present. Confirmed affected platforms include Windows 10 and Windows 11 (all supported versions) and Windows Server 2019, 2022, and 2025. Reported tests indicate the exploit functions with very high reliability — the original coverage describes near‑100% success even on systems that had received Microsoft’s April 2026 updates. That combination of broad platform reach and high reliability makes RedSun particularly concerning for enterprises where Defender is enabled by default.
Attribution, verification, and severity
Chaotic Eclipse published the vulnerability disclosure and exploit methodology publicly on GitHub; independent researcher Will Dormann independently confirmed the exploit’s effectiveness. The disclosure classifies the underlying weakness under CWE: Insufficient Granularity of Access Control and maps it to MITRE ATT&CK’s Privilege Escalation tactic. Reported severity metrics place the flaw in a high-risk category (reports reference a CVSS-style 7.8 rating), and the lack of an available patch at the time of disclosure elevates the urgency for defensive measures.
Immediate mitigation and detection strategies
- Monitor for anomalous Defender file write behavior, especially operations involving cldapi.dll that target C:WindowsSystem32 or other protected directories.
- Create endpoint detection rules to flag unusual use of opportunistic locks, file reparse points, or sudden writes to system binaries originating from non‑privileged processes.
- Audit and alert on changes to critical system binaries and service executables (for example, unexpected modifications to TieringEngineService.exe).
- Restrict who can create or manipulate NTFS reparse points and directory junctions via group policy and file system permissions where possible.
- Consider temporary hardening: limit local user write access contexts, apply stricter application control (e.g., blocklist unknown or unsigned binaries), and increase monitoring of Defender-related processes.
- Segregate sensitive hosts and apply least-privilege controls to reduce the blast radius if a local user compromise occurs.
Longer-term considerations for vendors and defenders
RedSun highlights a category of design risks when cloud-aware security components manipulate filesystem state automatically and under elevated privileges. Vendors should re-evaluate Defender’s cloud-file workflow to ensure operations that restore or rewrite files cannot be redirected to privileged locations, and they should add stronger validation of destination paths and privilege boundaries. For security teams, this disclosure is a reminder to treat trusted security agents as part of the attack surface: when an agent runs with elevated privileges, its file-handling logic becomes a potential escalation vector.
What to watch next
Keep an eye on Microsoft advisories for an official patch or mitigation guidance. Also monitor GitHub and security mailing lists for supplemental proof-of-concept details and for detection rules contributed by the research community. In the absence of a patch, proactive monitoring and strict endpoint controls are the most practical defenses against this high-impact vulnerability.

Recently Leaked Windows Zero-Days Now Being Actively Exploited: What You Need to Know
Threat actors have begun abusing three recently disclosed Windows vulnerabilities to escalate…
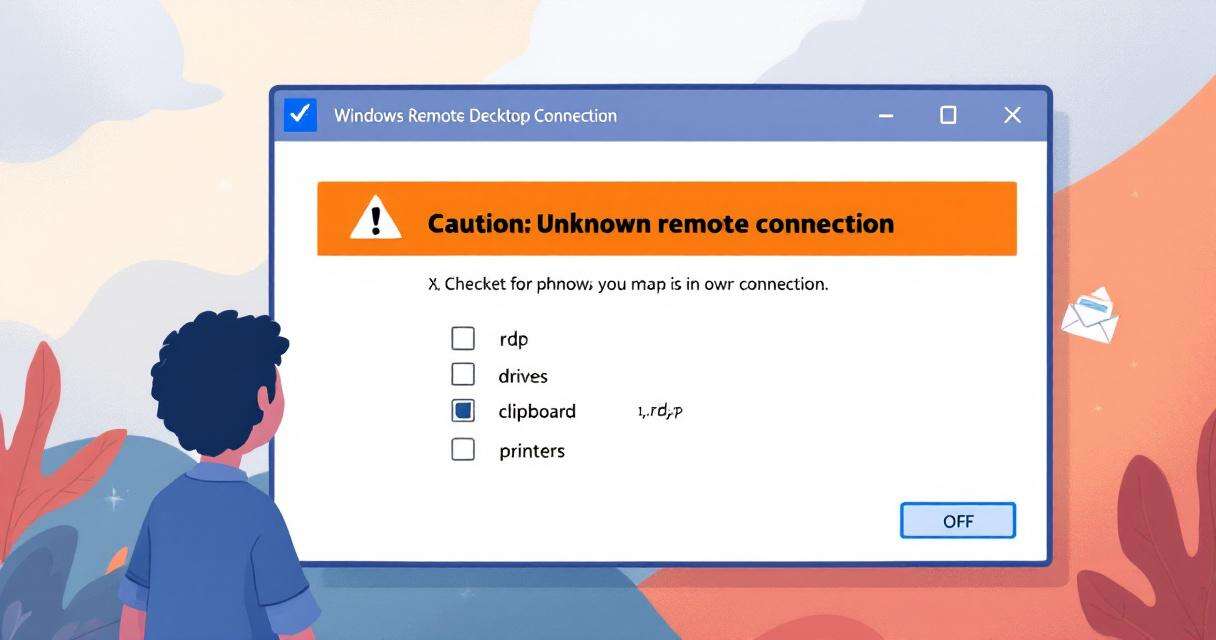
New RDP Alert After April 2026 Security Update Warns of Unknown Connections
Microsoft’s April 2026 Patch Tuesday introduced a small-looking but important change to…

Breaking the code: how a multi-stage “code of conduct” phishing campaign led to AiTM token compromise
Phishing has evolved from crude scams to carefully engineered deceptions that mimic…
Critical Microsoft 365 Copilot Flaws: What Organizations Need to Know
Microsoft has disclosed and silently remediated three critical information-disclosure vulnerabilities in Microsoft…