
In late 2025 and into early 2026, a sophisticated intrusion campaign used the everyday familiarity of Microsoft Teams to turn routine collaboration into a direct route for enterprise compromise. By posing as IT helpdesk staff and exploiting users’ trust in external Teams invitations, the threat group tracked as UNC6692 moved from a simple chat message to full domain-level access—without exploiting a software vulnerability. The result was a carefully staged, cloud-hosted operation that blended social engineering, browser-based credential harvesting, and a modular malware framework the researchers call the SNOW ecosystem.
How the UNC6692 Campaign Works
UNC6692’s campaign begins with social engineering built on volume and urgency. The attackers launched an email-bombing phase to overwhelm targets’ inboxes, then followed with a Microsoft Teams message from an external account posing as support to help with the “email issue.” That chat invitation, accepted by an employee, set the stage for a multi-phase web-based ruse that included a convincing phishing landing page, an authentication trick to capture strong passwords, and automatic installation of tools that established persistence and remote command capability.
The infection chain is notable for its choreography:
Phase 1 — Environment gating: Victims are forcibly redirected into Microsoft Edge using the microsoft-edge: URI and require a specific ?email= parameter in the URL to proceed, making the attack environment predictable and the exploit path reliable.
Phase 2 — Credential harvesting: A staged authentication prompt intentionally rejects the first two attempts to encourage a clean, accurate third entry—then exfiltrates credentials to attacker-controlled cloud storage.
Phase 3 — Distraction sequence: A fake progress UI masks real-time exfiltration while the victim believes a repair utility is running.
Phase 4 — Malware staging: AutoHotkey binaries and scripts download and execute, deploying a malicious browser extension and other components that anchor the attack.
The SNOW Malware Ecosystem
UNC6692’s toolkit—termed the SNOW ecosystem—is a modular, three-component framework designed to maintain persistence, tunnel traffic, and provide local command-and-control. Each piece plays a clear role in escalating from browser compromise to domain takeover.
| Component | Type | Role |
|---|---|---|
| SNOWBELT | JavaScript browser extension | Initial foothold; intercepts and relays C2 commands; uses DGA-based S3 URLs for C2 |
| SNOWGLAZE | Python-based WebSocket tunneler | Routes TCP traffic through the victim via a SOCKS proxy to a Heroku C2 server |
| SNOWBASIN | Python local HTTP server (port 8000) | Executes shell commands, captures screenshots, exfiltrates files |
SNOWBELT (the malicious Chromium extension) establishes the initial foothold and communicates with C2 locations that are dynamically generated and hosted on reputable cloud platforms. Persistence is achieved through multiple mechanisms: startup folder shortcuts, scheduled tasks, and headless Edge processes silently loading the extension. SNOWGLAZE tunnels traffic by wrapping data in Base64-encoded JSON over WebSockets, making command traffic look like normal encrypted web sessions. SNOWBASIN runs locally to execute commands, capture screenshots, and stage files for exfiltration.
Living off the Cloud: Why This Attack Evades Traditional Defenses
A defining characteristic of the campaign is the extensive use of legitimate cloud services—AWS S3 for payload and credential storage, Heroku for C2 endpoints, and broadly trusted HTTPS channels for communications. By “living off the cloud,” attackers make malicious activity blend into normal, high-volume encrypted web traffic. IP and domain reputation filtering become far less effective when attackers use well-known cloud providers; similarly, encrypted channels and WebSocket traffic can obscure anomalous patterns from traditional network monitoring.
This approach forces defenders to shift focus: rather than relying solely on network indicators, organizations must increase scrutiny of browser behavior (especially extensions and headless browser processes), cloud egress activity (unusual S3 access patterns, new or unexpected buckets), and user interactions that override security prompts. Restricting external Teams access and educating staff to treat unsolicited help links skeptically are immediate mitigations that can break the attack chain at the earliest stage.
From Browser Compromise to Domain Controller: The Escalation Path
Once established on a host, UNC6692 scanned internal networks for common Windows ports (135, 445, 3389) and used lateral tools and legitimate admin utilities to move across systems. The attackers used PsExec routed through the SNOWGLAZE tunnel to reach a backup server, where they dumped LSASS memory to harvest credential hashes. Those hashes were processed offline and then used in Pass-the-Hash attacks to authenticate directly to domain controllers.
On domain controllers, the adversary extracted the Active Directory database (NTDS.dit) and critical registry hives (SAM, SYSTEM, SECURITY), effectively harvesting the “crown jewels” required for persistent, pervasive control of the environment. Screenshots captured during the operation confirmed targeted use of forensic/forging utilities such as FTK Imager, and all high-value artifacts were exfiltrated to cloud-hosted endpoints.
Indicators of Compromise (what to look for)
Researchers published specific IOCs that defenders can use to hunt for this campaign’s artifacts:
- Phishing URL pattern: https://service-page-[ID]-outlook.s3.us-west-2.amazonaws.com/update.html?email=
- C2 WebSocket: wss://sad4w7h913-b4a57f9c36eb[.]herokuapp[.]com:443/ws
- SNOWBELT C2 URL pattern: https://[a-f0-9]{24}-[0-9]{6,7}-[0-9]{1}.s3.us-east-2.amazonaws[.]com
- SNOWBELT VAPID key (example): BJkWCT45mL0uvV3AssRaq9Gn7iE2N7Lx38ZmWDFCjwhz0zv0QSVhKuZBLTTgAijB12cgzMzqyiJZr5tokRzSJu0
- Masquerading filenames: RegSrvc.exe (AutoHotKey binary), Protected.ahk, SysEvents (SNOWBELT extension directory)
Practical Recommendations for Defenders
- Harden collaboration settings: Limit or tightly control external tenants in Microsoft Teams. Where possible, require additional verification before accepting external chats that initiate links or file transfers.
- Monitor browser extension activity: Track the installation of unsigned or unexpected Chromium extensions, unusual headless browser processes, and extensions that maintain persistent background connections.
- Inspect cloud egress: Alert on unusual S3 bucket writes from endpoints, especially new buckets or buckets that match DGA-like patterns. Correlate cloud storage access with endpoint behavior.
- Expand telemetry: Capture browser-level events, credential prompt failures, and the use of microsoft-edge: URI redirects in logs. These signals can expose the gating and credential-harvesting phases.
- Segment and protect backups: Limit administrative access to backup servers and monitor for process dumps or unexpected forensic tool execution. Enforce multi-factor authentication for privileged tasks and consider protecting LSASS memory access.
- Train users on social engineering through collaboration tools: Simulated exercises should include Teams-based phishing scenarios; users should verify helpdesk requests through separate channels before executing patches or utilities.
Conclusion
UNC6692’s campaign is a reminder that attackers will exploit the most trusted tools when defenders assume those channels are safe. By weaponizing Microsoft Teams and weaving cloud services into every stage of their operation, these adversaries turned routine collaboration into a gateway for full enterprise compromise. Stopping similar campaigns requires a blend of technical controls—browser and cloud telemetry, stricter Teams policies—and user-focused defenses that make it harder for a convincing chat to become a catastrophic breach.

Breaking the code: how a multi-stage “code of conduct” phishing campaign led to AiTM token compromise
Phishing has evolved from crude scams to carefully engineered deceptions that mimic…
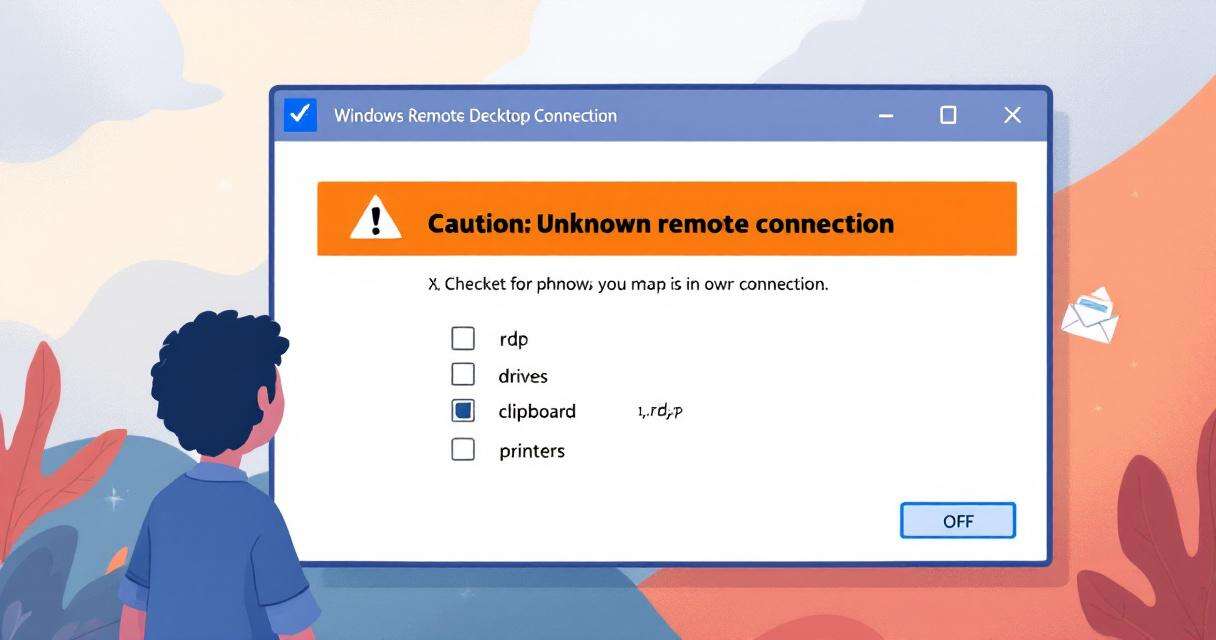
New RDP Alert After April 2026 Security Update Warns of Unknown Connections
Microsoft’s April 2026 Patch Tuesday introduced a small-looking but important change to…
Critical Microsoft 365 Copilot Flaws: What Organizations Need to Know
Microsoft has disclosed and silently remediated three critical information-disclosure vulnerabilities in Microsoft…

Lovable AI App Builder Reportedly Exposes Thousands of Projects’ Source Code and Customer Data
A critical Broken Object Level Authorization (BOLA) vulnerability in Lovable, an AI-powered…