A security researcher using the handle Chaotic Eclipse has publicly released a working proof‑of‑concept for a Windows zero‑day local privilege escalation (LPE) exploit called “BlueHammer.” The disclosure, accompanied by full source code on GitHub, was confirmed as functional by vulnerability researcher Will Dormann and demonstrates that a low‑privileged local user can escalate to NT AUTHORITYSYSTEM on affected machines. The release has sparked concern across the security community because it is an uncoordinated disclosure: the exploit is live before Microsoft has issued a patch or assigned a CVE.
What the exploit does
BlueHammer enables a local, nonadministrative user to gain full SYSTEM privileges on a Windows host. In demonstrations shared by the researcher and verified by others, a command prompt started from a limited user directory (for example, C:UserslimitedDownloads>) quickly transitions to a SYSTEM shell, with whoami returning NT AUTHORITYSYSTEM. The PoC output also shows credential‑harvesting behavior, including NTLM hashes for local accounts and indications that administrative account credentials can be exposed. The exploit was shown running on a Windows 11 machine (Build 10.0.26200.8037), which suggests modern, fully updated systems can be affected.
Why this disclosure matters
Local privilege escalation vulnerabilities are particularly dangerous because they allow attackers who already have limited access—through a phishing success, a malicious insider, or a less privileged malware component—to elevate their privileges to the highest level on a system. Once SYSTEM access is achieved, an attacker can disable security controls, install persistent backdoors, read or modify any file, and move laterally across networks. The immediate public availability of working PoC code increases the likelihood that criminal groups and advanced persistent threat (APT) actors will integrate and refine the exploit rapidly.
Motivation behind the public release
Chaotic Eclipse cited frustration with Microsoft’s Security Response Center (MSRC) as the reason for the public release. According to the researcher, reporting processes had become onerous and slow, in part due to staff changes and rigid procedural requirements. The disclosure noted that MSRC requested a video demonstration as part of the reporting process—a step the researcher described as unusual and potentially obstructive. Feeling the report stalled or mishandled, the researcher opted for an uncoordinated disclosure, a route some researchers take when they believe vendor remediation is not progressing.
Reliability and real‑world use
The researcher acknowledged BlueHammer is not 100% reliable in all environments but stated it “works well enough” to be operationally useful. Even partially reliable LPE exploits can be refined by skilled attackers and weaponized across large toolsets. Historically, publicly released PoC code is often adapted by ransomware groups and other threat actors within days, increasing urgency for defenders to act even before an official patch is released.
Immediate mitigations and defensive steps
Until Microsoft provides a patch or advisory, organizations should adopt layered mitigations and heightened monitoring:
- Minimize local administrative privileges: Enforce least privilege across endpoints and remove unnecessary local admin rights from user accounts.
- Harden endpoint detection: Tune EDR and antivirus solutions to detect unusual processes spawning SYSTEM shells, unexpected privilege escalations, and attempts to access local SAM or credential stores.
- Enable and analyze enhanced logging: Centralize Windows event logs and look for anomalous token manipulations, process creations, and credential dumping indicators.
- Apply strict application control: Use tools like AppLocker or Windows Defender Application Control to limit which binaries and scripts can run.
- Isolate high‑value systems: Segregate sensitive servers and endpoints and restrict lateral movement paths.
- Monitor public sources: Watch for official Microsoft advisories, CVE assignments, and updated detection guidance.
What security teams should plan next
- Incident readiness: Ensure playbooks cover local privilege escalation investigations, including steps to capture forensic artifacts before remediation changes the scene.
- Patch management posture: Prioritize testing and rapid deployment of any Microsoft updates that address this vulnerability.
- Threat intelligence: Share indicators of compromise (IOCs) internally and with trusted partners; correlate with network and endpoint telemetry for early detection.
- User education: Remind users about phishing and social engineering risks that commonly precede local access compromises.
What this means for vendors and researchers
This episode highlights friction between researchers and coordinated vulnerability disclosure processes. While vendors must balance thorough triage with timely remediation, researchers can escalate to public disclosure when they believe a report is stalled. Both communities benefit when reporting channels are responsive, transparent, and collaborative—reducing the incentive for uncoordinated drops that place users at risk.
Conclusion
BlueHammer is a concerning example of a functional local privilege escalation exploit released into the wild. Its public PoC raises immediate risk for organizations with exposed or insufficiently hardened endpoints. Until Microsoft issues a patch or mitigation steps, defenders must assume the exploit can be weaponized and take proactive measures: reduce local privileges, strengthen detection, and prepare incident response capabilities. The broader lesson is that effective, timely collaboration between researchers and vendors is critical to user safety; when that collaboration breaks down, risk increases for everyone.

RedSun: New Microsoft Defender Zero-Day Lets Unprivileged Users Gain SYSTEM Access
A freshly disclosed zero-day vulnerability in Microsoft Defender, dubbed "RedSun," has raised…

Recently Leaked Windows Zero-Days Now Being Actively Exploited: What You Need to Know
Threat actors have begun abusing three recently disclosed Windows vulnerabilities to escalate…
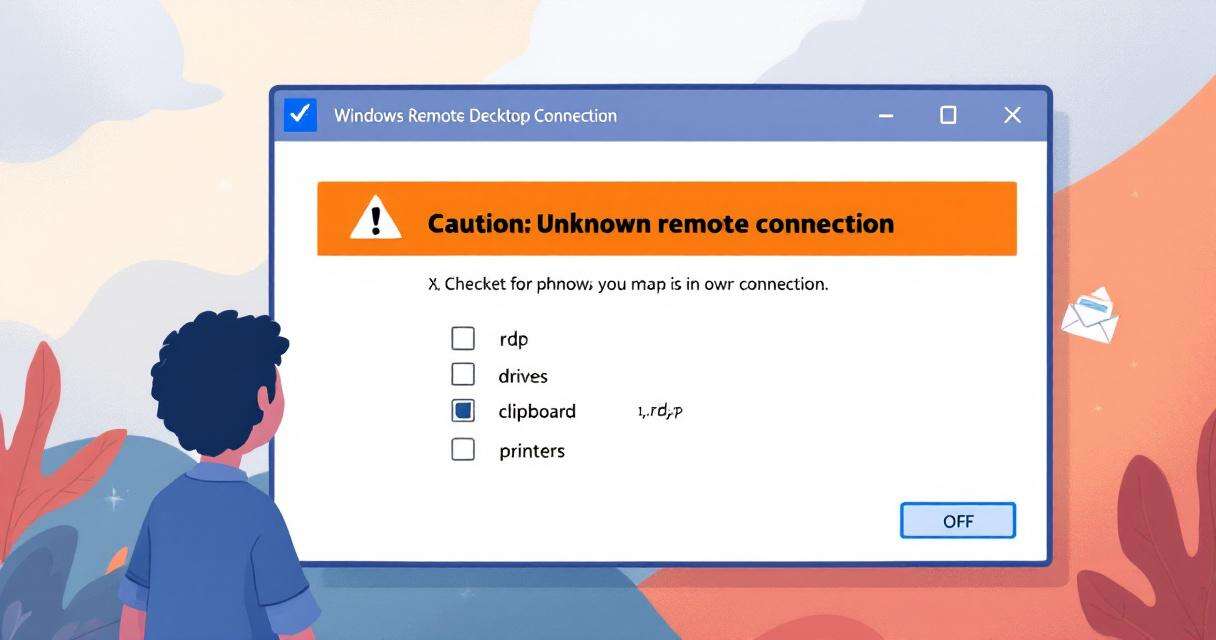
New RDP Alert After April 2026 Security Update Warns of Unknown Connections
Microsoft’s April 2026 Patch Tuesday introduced a small-looking but important change to…

Breaking the code: how a multi-stage “code of conduct” phishing campaign led to AiTM token compromise
Phishing has evolved from crude scams to carefully engineered deceptions that mimic…