
A recently disclosed vulnerability in the popular Ninja Forms “File Upload” addon has placed roughly 50,000 WordPress sites at risk of full takeover. Tracked as CVE-2026-0740 and carrying a CVSS score of 9.8, the flaw allows unauthenticated arbitrary file uploads — a straightforward path to remote code execution (RCE) for attackers. Site owners who rely on the affected plugin must act immediately to patch and inspect their environments.
What happened
Security researcher Sélim Lanouar discovered the issue and reported it, receiving a bug bounty for the find. The problem resides in the plugin’s file-handling logic: when user-uploaded files are processed, the plugin attempts to verify the original file type but fails to validate the destination filename’s extension during the move_uploaded_file() operation. Combined with insufficient filename sanitization, this oversight enables path traversal and allows an attacker to place executable PHP files into the website root or other sensitive locations. Once a webshell is uploaded and executed, attackers can run arbitrary commands, exfiltrate databases, inject malware, or pivot to other systems.
Why this is severe
An unauthenticated arbitrary file upload means attackers do not need credentials to exploit the site — they only need to be able to reach the vulnerable endpoint. The high CVSS score reflects the ease of exploitation and the catastrophic impact of a successful RCE. Automated scanning tools and malicious bots routinely probe WordPress sites for such weaknesses, so unpatched installations can be compromised quickly and at scale.
How the vulnerability works (at a glance)
- The plugin handles uploads via a handle_upload() function that ultimately moves the temporary file to a final directory using move_uploaded_file().
- The code validates the original file type but neglects to sanitize or enforce the destination filename’s extension when performing the move.
- Attackers exploit this by manipulating the upload path (path traversal) and saving files with .php extensions in web-accessible locations.
- Executing the uploaded PHP file yields a webshell, granting command execution on the server.
Scope and timeline
- Affected versions: All versions up to and including 3.3.26.
- Partial mitigation was introduced in version 3.3.25; a complete patch was released in version 3.3.27 on March 19, 2026.
- Wordfence deployed firewall rules for premium users on January 8, 2026, and extended protections to free users by February 7, 2026.
- Despite protections and patches, many sites may still be running vulnerable versions and remain susceptible to automated exploitation.
Immediate actions for site owners
- Update Now: Upgrade the Ninja Forms File Upload addon to version 3.3.27 or later. This is the single most important step.
- If you cannot update immediately: Disable or remove the addon until you can apply the patch. Reducing attack surface is critical.
- Scan for webshells and suspicious files: Search your webroot and upload directories for recently added .php files or files with odd names. Pay attention to directory traversal patterns.
- Review logs: Check access logs for suspicious POSTs to upload endpoints, unusual requests, or connections executing uploaded scripts.
- Restore and rotate credentials: If you find signs of compromise, restore from a known-good backup, rotate database and admin credentials, and revoke API keys or tokens that may have been exposed.
- Apply WAF rules: If you have a web application firewall (WAF) or security plugin, ensure it includes protections for this vulnerability or block suspicious upload activity.
- Monitor: Increase monitoring for anomalous activity and set up file integrity checks.
Detection tips and indicators of compromise
- Unexpected .php files in wp-content/uploads, plugin directories, or webroot.
- Unusual spikes in POST requests to form-related endpoints.
- New admin users, altered pages, unexpected redirects, or injected JavaScript.
- Outbound connections from the web server that are not accounted for.
- Elevated CPU or I/O usage coinciding with unknown processes.
Longer-term hardening measures
- Principle of least privilege: Ensure upload directories and the web server run with the minimum permissions needed. Prevent direct execution of scripts in upload directories via server configuration (e.g., disable PHP execution in wp-content/uploads).
- Content validation: Rely on server-side MIME-type checks, strict extension whitelists, and filename sanitization for all uploads.
- Regular patching: Keep WordPress core, themes, and plugins updated and subscribe to vulnerability feeds for quick remediation.
- Backups and recovery plans: Maintain frequent, tested backups stored off-site to recover quickly in case of compromise.
- Defense in depth: Combine WAFs, intrusion detection, endpoint security, and regular audits to reduce risk exposure.
For incident responders
- If you suspect a compromise:
- Isolate the affected host from the network where feasible.
- Collect disk images and logs for forensic analysis before making changes.
- Identify scope by enumerating modified files and new accounts.
- Restore to a clean baseline and harden the environment before reconnecting.
- Notify stakeholders and, if required, follow any regulatory disclosure procedures.
Final thoughts
CVE-2026-0740 is a textbook example of how a small oversight in file handling can have outsized consequences. Because the vulnerability requires no authentication and is easy to weaponize, site owners must prioritize patching and systematic checks. Updating to Ninja Forms File Upload version 3.3.27 or later, scanning for signs of compromise, and applying basic hardening steps will dramatically reduce risk.
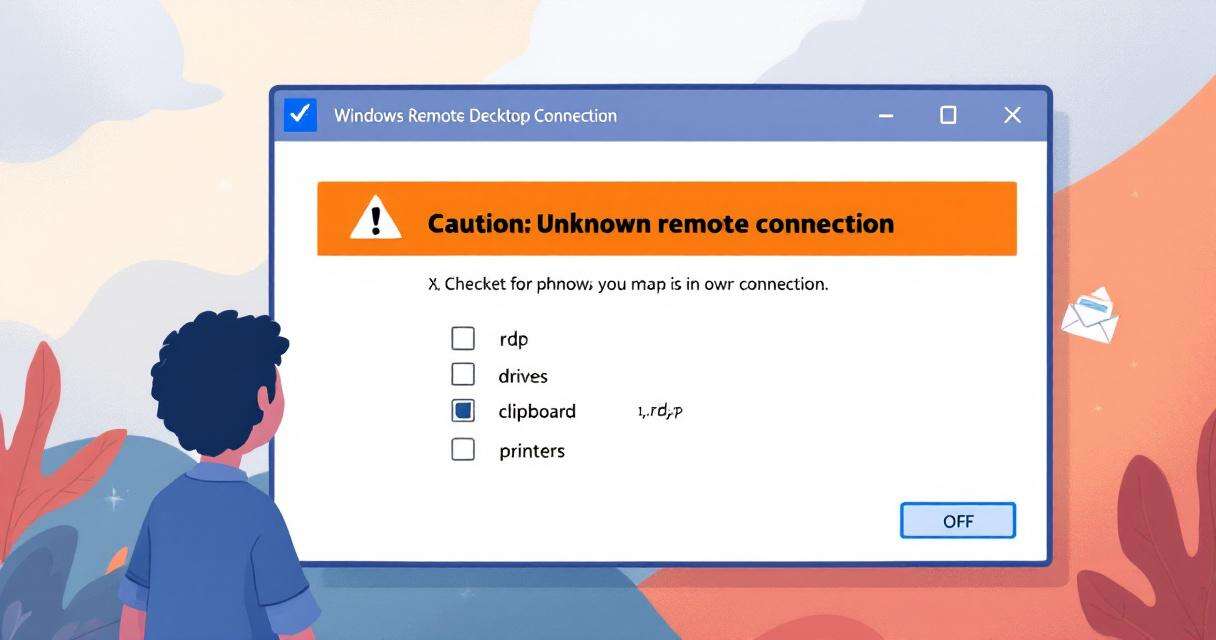
New RDP Alert After April 2026 Security Update Warns of Unknown Connections
Microsoft’s April 2026 Patch Tuesday introduced a small-looking but important change to…

RedSun: New Microsoft Defender Zero-Day Lets Unprivileged Users Gain SYSTEM Access
A freshly disclosed zero-day vulnerability in Microsoft Defender, dubbed "RedSun," has raised…

One-Click RCE in Azure Windows Admin Center: what happened and what you need to do
Windows Admin Center (WAC) is a convenient, browser-based management hub for administrators…
Project Glasswing and Mythos Preview: What 10,000+ AI-Found Vulnerabilities Mean for Software Security
In the weeks since Anthropic unveiled Project Glasswing and the Mythos Preview…