
Microsoft released fixes earlier this year for CVE-2026-21510, a security feature bypass in Windows Explorer that let specially crafted shortcut (LNK) files execute a remotely hosted DLL without the usual security warning. Researchers observed exploitation in the wild and uploaded a sample to malware repositories, enabling vendors and defenders to reproduce the issue and protect legacy systems that no longer receive timely official updates. This post explains how the vulnerability worked, what Microsoft changed, how 0patch addressed it for older Windows installations, and practical steps administrators can take now.
How the vulnerability worked
Normally, when a user double‑clicks a shortcut that comes from the internet (marked with the “mark-of-the-web”) or resides on an untrusted network share, Explorer shows a security prompt warning about the shortcut’s origin. CVE-2026-21510 allowed a crafted LNK file associated with the “All Control Panel Items” GUID to bypass that check and directly load a remote DLL without showing any warning. In short: a user could be tricked into launching code stored on a remote host with no visible indication of risk. The flaw stemmed from how the Control Panel GUID path handling delegated to shortcut-processing code without applying the same mark-of-the-web / zone checks that were expected.
Microsoft’s official patch
Microsoft addressed the issue by extending windows.storage.dll with a new data structure and a dedicated callback path for Control Panel shortcut handling. That callback explicitly inspects both the shortcut file and its target for mark-of-the-web, ensuring that the same origin and zone protections apply to Control Panel–related shortcuts as they do elsewhere. Prior to this change, only the target binary (for example, C:WindowsSystem32rundll32.dll) was being examined for web-origin metadata, which left the shortcut itself unchecked in certain launching paths.
How 0patch’s micropatch works
0patch implemented a simpler, targeted fix that operates inside the CShellLink::_InvokeDirect function. The micropatch looks at the local variable holding the shortcut path, checks that the file has a “.lnk” extension, and runs MapUrlToZone on that path. MapUrlToZone reveals whether a path is considered untrusted (including mark-of-the-web). If the shortcut is from an untrusted location or contains web-origin metadata, the micropatch triggers a security warning so the user can decide whether to continue. The approach also allows trusted network locations to be whitelisted via Internet Options (Trusted Sites), giving admins control over when the warning should be suppressed.
Which systems are covered by the micropatch
0patch prepared micropatches for a broad set of Windows releases so organizations running out-of-support or legacy systems can be protected without waiting for official updates. Covered systems include (but are not necessarily limited to):
- Windows 11 v22H2 and v21H2 (fully updated)
- Windows 10 v22H2, v21H1, v20H2, v2004, v1909, v1809, v1803 (fully updated)
- Windows 7 (fully updated) and Windows Server 2008 R2 (fully updated), as well as Server 2012 and 2012 R2 where applicable
0patch reports that these micropatches have already been distributed to online endpoints running 0patch Agent under PRO or Enterprise accounts unless group policies prevented automatic application.
Practical implications and recommendations
This vulnerability highlights how subtle pathway differences (in this case, how Control Panel GUIDs are processed) can lead to serious bypasses of security UX designed to protect end users. Administrators and security teams should:
- Ensure endpoints have either Microsoft’s patch applied or equivalent mitigations in place.
- For organizations using legacy Windows builds beyond official support, evaluate runtime patching options such as 0patch to cover high‑risk gaps.
- Educate users about the risks of opening shortcuts from untrusted shares or the internet, and consider locking down ability to run shortcuts from network locations where possible.
- Use Group Policy and Internet Options to explicitly trust only sanctioned network locations, minimizing false positives while retaining protection.
How to get protected now
If you’re unfamiliar with 0patch, you can create a free account on 0patch Central, start a trial, and install the 0patch Agent. For PRO and Enterprise deployments the agent can automatically receive and apply micropatches without reboots. For organizations that prefer official fixes, ensure Microsoft’s updates that introduce the windows.storage.dll changes are fully deployed across your estate.
Conclusion
CVE-2026-21510 was a practical example of how a seemingly small sidestep in path handling can allow remote code to run without user warning. Microsoft’s structural fix in windows.storage.dll corrects the underlying handling, while 0patch’s micropatch offers an immediate, compatible protection path for many legacy and supported Windows releases. Administrators should verify that either the official patch or a trusted micropatch has been applied and continue to enforce policies that reduce users’ exposure to untrusted shortcuts.

Breaking the code: how a multi-stage “code of conduct” phishing campaign led to AiTM token compromise
Phishing has evolved from crude scams to carefully engineered deceptions that mimic…
Critical Microsoft 365 Copilot Flaws: What Organizations Need to Know
Microsoft has disclosed and silently remediated three critical information-disclosure vulnerabilities in Microsoft…

Hackers Leverage Microsoft Teams to Breach Organizations: Inside UNC6692’s SNOW Campaign
In late 2025 and into early 2026, a sophisticated intrusion campaign used…
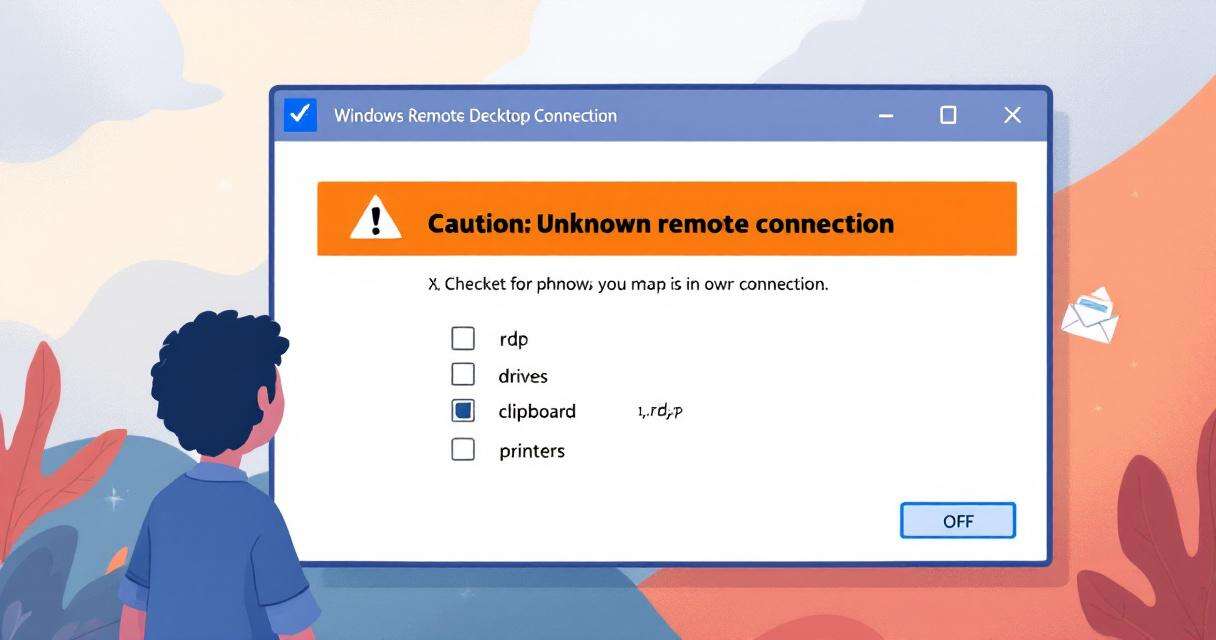
New RDP Alert After April 2026 Security Update Warns of Unknown Connections
Microsoft’s April 2026 Patch Tuesday introduced a small-looking but important change to…