AI-powered chatbots and assistants for health are proliferating. In recent months major technology companies have launched or expanded consumer-facing tools that let people ask medical questions, connect health records, or receive triage-style guidance. These products promise greater access to health information, but independent researchers and clinicians warn that rigorous, third‑party evaluation of their safety and effectiveness remains limited. The landscape
Author: Saugata Datta
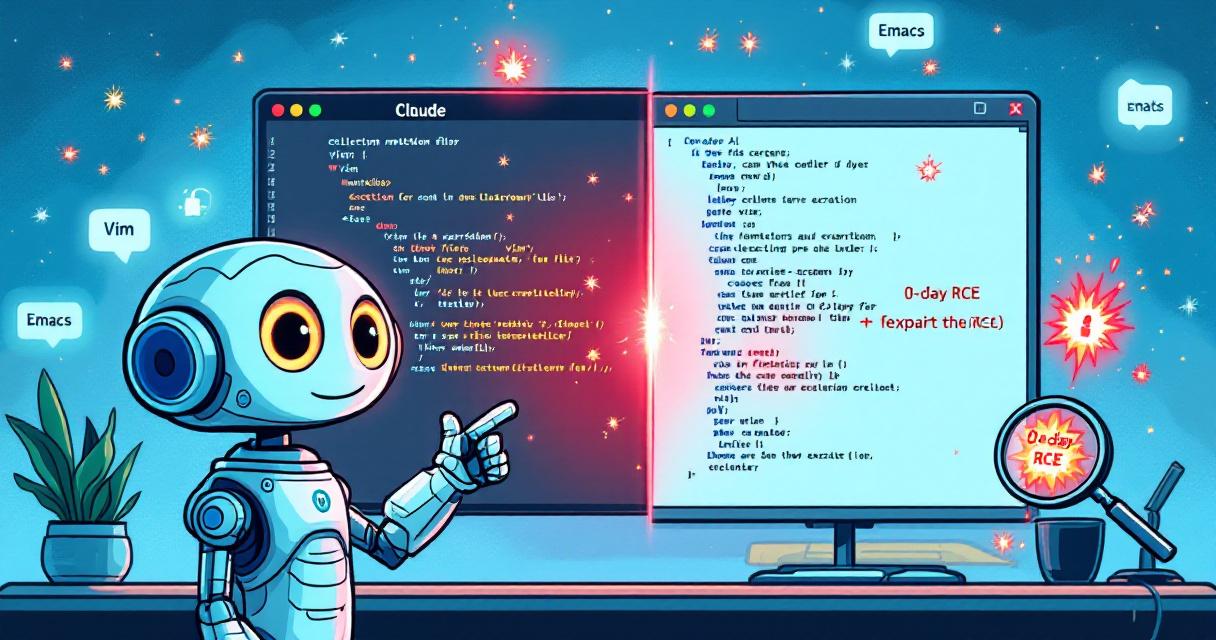
Claude AI Uncovers Zero-Day RCEs in Vim and Emacs — A Turning Point for Bug Hunting
A recent research effort demonstrated that advanced AI models can accelerate and amplify vulnerability discovery in legacy software. Anthropic’s Claude was used to hunt for remote code execution (RCE) flaws and successfully produced proof-of-concept exploits against both Vim and GNU Emacs. The findings illustrate how natural-language prompts can surface high-impact bugs with surprising ease, and they raise urgent questions about
What’s New in Microsoft Defender: AI Triage, Predictive Hardening, and Call Monitoring — What IT Teams Should Know
Microsoft used RSA 2026 to roll out a wave of Defender enhancements that are already changing how security teams detect, investigate, and respond to risk. The announcements bundle intuitive UX changes—like a consolidated identity dashboard—with more consequential shifts: AI-driven triage and automated hardening that can act proactively on predicted attacker movement. These features promise speed and scale, but they also
Anthropic’s Mythos Rocks Cybersecurity Stocks: What Investors and Defenders Need to Know
News moved fast one Friday: a new, exceptionally powerful AI model from Anthropic—codenamed Mythos—leaked into the market conversation, and the ripple effects were immediate. Stocks tied to cybersecurity fell sharply, reflecting a fresh wave of anxiety: if an AI can find complex code flaws faster than teams of humans, what becomes of the companies that sell digital defenses? This post
AI for Nuclear Energy — Powering an Intelligent, Resilient Future
The world’s surge in power demand is colliding with an energy infrastructure that was largely designed for an analog age. Meeting that demand with clean, reliable power requires more than ambition; it requires faster, repeatable delivery of complex projects. Nuclear energy is central to that future, but development timelines, fragmented data, and heavy regulatory processes create persistent bottlenecks. Artificial intelligence,
OpenAI Brings Plugins to Codex, Narrowing the Gap with Claude Code
OpenAI has quietly expanded Codex’s capabilities by adding a plugins system — a move that makes the coding assistant feel less like a standalone tool and more like a configurable platform. On the surface, these plugins are collections that can include workflow “skills,” integrations with external applications, and connections to MCP (Model Context Protocol) servers. For users, the most immediate