Attackers and defenders are now playing with the same toys: powerful AI models that can find and exploit zero-day vulnerabilities in hours. At Google Cloud Next ’26, Google and Wiz unveiled a set of AI-driven defenses designed to shrink the time between discovery and remediation — and to automate much of the manual work that has left security teams lagging
Category: Cybersecurity
Zero-Day, APT, Exfiltration, Lateral-Movement, Privilege-Escalation, Botnet, Rootkit, Backdoor, Keylogger, Smishing, Vishing, Spear-Phishing, Social-Engineering, MITM, SQL-Injection, XSS, CSRF, Path-Traversal, Buffer-Overflow, Honeypot, CVE, CVSS, Red-Team, Blue-Team, Threat-Hunting, Malware-Analysis, MITRE-ATT&CK, Insider-Threat, Jailbreak, Shellcode, Exploit-Kit, LFI, RFI, Obfuscation, Payload, security advisory, vulnerability disclosure, CWE, OWASP, cybersecurity news, threat intelligence, SOC, SIEM, cryptotheft, evasion, CVE Security
Comment and Control: How GitHub Comments Became a New Prompt-Injection Threat
A new class of prompt-injection attacks—dubbed “Comment and Control”—turns GitHub pull requests, issues, and comments into attack surfaces that can hijack AI coding agents and siphon secrets directly from CI/CD environments. Unlike classic prompt injection that waits for a user to feed a document to an agent, this pattern is proactive: opening a PR or posting an issue can automatically
Lovable AI App Builder Reportedly Exposes Thousands of Projects’ Source Code and Customer Data
A critical Broken Object Level Authorization (BOLA) vulnerability in Lovable, an AI-powered app builder, has reportedly left thousands of legacy projects accessible to unauthorized users. According to security researchers, an API endpoint returned full project data — including source code, database credentials, AI chat histories, and customer information — for projects created before November 2025. While Lovable appears to have
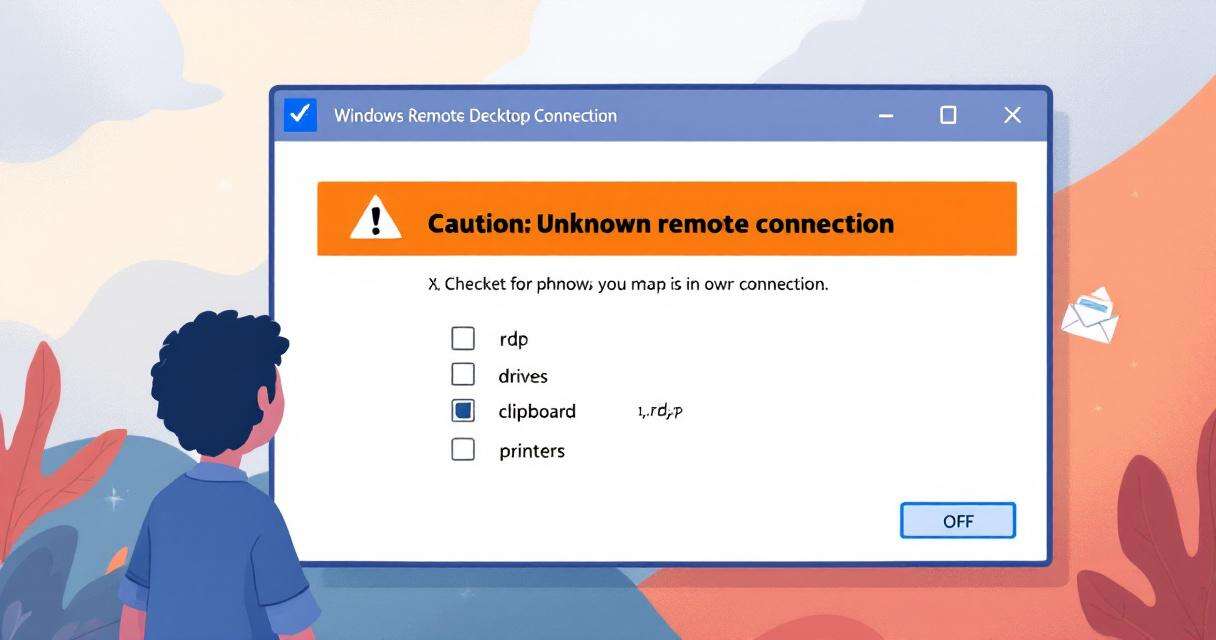
New RDP Alert After April 2026 Security Update Warns of Unknown Connections
Microsoft’s April 2026 Patch Tuesday introduced a small-looking but important change to how Windows handles Remote Desktop (.rdp) files. What used to be a silent, one-click experience can now surface clear warnings about unknown connections and requested local resource access, closing an easy door attackers have been exploiting for phishing and session hijacking. For organizations and individual users alike, the
Recently Leaked Windows Zero-Days Now Being Actively Exploited: What You Need to Know
Threat actors have begun abusing three recently disclosed Windows vulnerabilities to escalate privileges and interfere with Microsoft Defender, shifting a theoretical disclosure debate into a real-world security crisis. A security researcher known as “Chaotic Eclipse” (also called “Nightmare-Eclipse”) released proof-of-concept exploit code for all three flaws earlier this month, and multiple security teams have since observed the techniques used in
RedSun: New Microsoft Defender Zero-Day Lets Unprivileged Users Gain SYSTEM Access
A freshly disclosed zero-day vulnerability in Microsoft Defender, dubbed “RedSun,” has raised alarms across enterprise security teams: an unprivileged user can escalate to full SYSTEM-level access on fully patched Windows systems. The flaw was detailed publicly in April 2026 by a researcher known as “Chaotic Eclipse” (also referenced as Nightmare‑Eclipse on GitHub). Independent verification from vulnerability analyst Will Dormann confirms