Aura, the consumer digital safety company known for identity protection and fraud monitoring, recently confirmed a data breach that exposed nearly 900,000 marketing contacts. What seems like a single shocking number actually reveals deeper problems: legacy data inherited through acquisitions, the continued effectiveness of social-engineering attacks, and the tricky line between marketing lists and active customer records. This incident is
Category: Data Breach
Data Breach, data breach alert, data leak, data leakage, security incident, breach investigation, breach response, credential leak, personal data exposure, data theft, leaked database, exposed records, account compromise, password leak, corporate data breach, remote code execution, cyber espionage
Stryker Confirms Massive Wiper Strike — Thousands of Devices Erased in Alleged Iran-Linked Operation
Stryker, the global medical technology company, confirmed on March 11, 2026, that it suffered a significant, destructive cyberattack that disabled large parts of its corporate Microsoft environment and resulted in the wiping of thousands of devices. The company characterized the incident as a deliberate data-destruction operation rather than a ransomware extortion scheme, and investigators and security firms have pointed to
Cognizant’s TriZetto Subsidiary Reports Data Breach Affecting 3.4 Million Patients
TriZetto Provider Solutions, a healthcare-technology subsidiary of Cognizant, has disclosed a large data breach that exposed the protected health information of 3,433,965 patients. The company classified the incident as an external system hacking event after threat actors gained unauthorized access to TriZetto’s external infrastructure. Timeline and discovery Initial unauthorized access occurred on November 19, 2024. TriZetto did not detect the
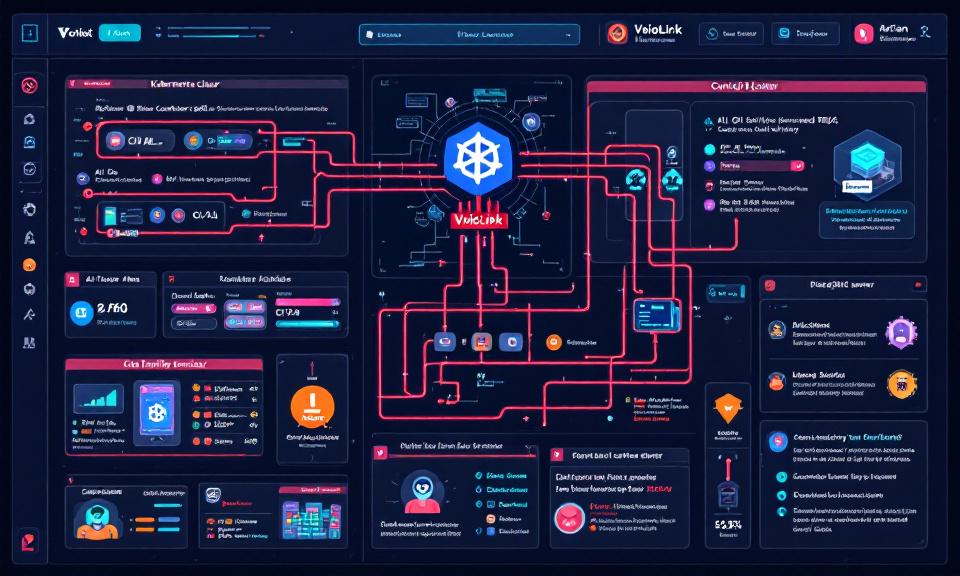
VoidLink Malware Framework: Key Points on How It Targets Kubernetes and AI Workloads
Title: VoidLink Malware Framework: Key Points on How It Targets Kubernetes and AI Workloads Overview VoidLink is a modular malware framework observed targeting cloud-native environments, with emphasis on Kubernetes clusters and AI infrastructure. Goal: persistence, lateral movement, data exfiltration, and abuse of compute (e.g., model theft, crypto-mining, or training/serving misuse). Modularity enables plugins for container escape, kubeconfig harvesting, and targeted
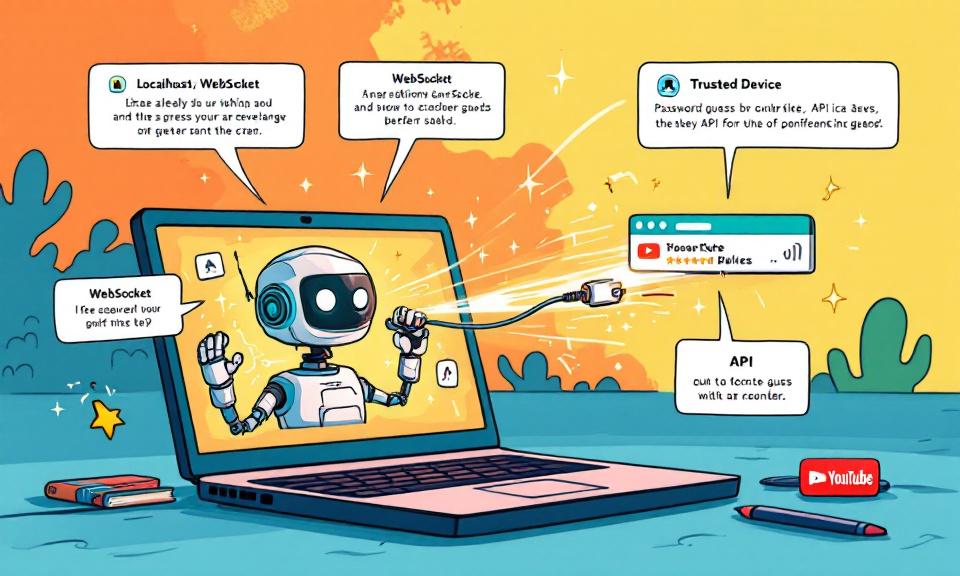
When Local Trust Breaks: The OpenClaw 0-Click Vulnerability and What Developers Must Do Now
The speed at which developer-facing AI agents have been adopted is staggering — and rapid adoption often outpaces secure design. A recent, high-impact vulnerability in OpenClaw demonstrates how a single innocuous browser visit can be transformed into a full agent takeover. For developers and security teams, this is a reminder that conveniences like “localhost-first” assumptions carry real risk. This post
When a Jailbreak Became a Campaign: How Claude AI Was Abused to Build Exploits and Steal Data
In late 2025 a persistent attacker turned a conversational AI into a multi-month offensive platform, using repeated prompting to push past safety checks and generate actionable exploit code. The incident — uncovered by a security firm and reported in mainstream sources — illustrates a worrying new vector in which AI models can be manipulated into performing the research, coding, and