The concept of a “smart home” once sounded futuristic, but today, it’s quickly becoming part of ordinary life. A smart home ecosystem is more than just a collection of cool gadgets—it’s about seamlessly integrating devices to work together, make routines easier, and unlock conveniences that were hard to imagine just a decade ago. Whether you’re dimming the lights with a
Category: Security
Zero-Day, APT, Exfiltration, Lateral-Movement, Privilege-Escalation, Botnet, Rootkit, Backdoor, Keylogger, Smishing, Vishing, Spear-Phishing, Social-Engineering, MITM, SQL-Injection, Cross-Site-Scripting, XSS, CSRF, Path-Traversal, Buffer-Overflow, Honeypot, CVE, CVSS, Red-Team, Blue-Team, Threat-Hunting, Malware-Analysis, MITRE-ATT&CK, Insider-Threat, Privilege-Flaw, Jailbreak, Shellcode, Exploit-Kit, LFI, RFI, Obfuscation, Payload.
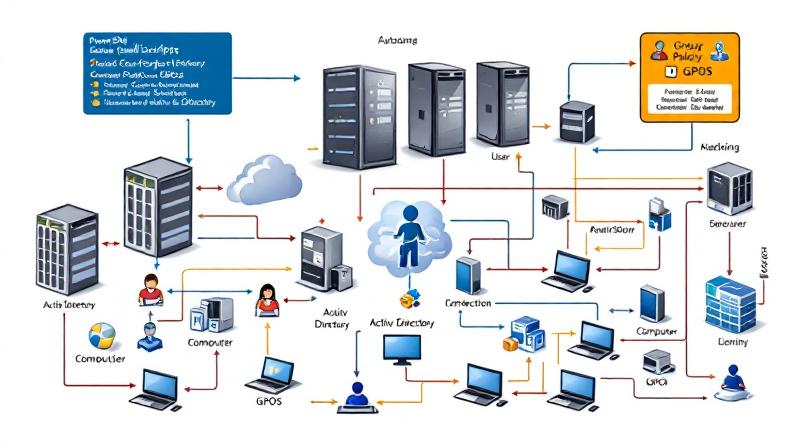
How to Automate GPO Tasks in Active Directory: PowerShell Techniques with Practical Examples
Automating Group Policy Object (GPO) tasks in Active Directory is critical for large organizations and IT administrators managing a high volume of policies. PowerShell provides enterprise-grade automation capabilities to create, modify, and deploy GPOs efficiently, reducing manual effort and minimizing errors. This guide dives deep into automating GPO management with PowerShell, showing step-by-step scripting techniques for both user and computer
The Ultimate Command Center for AdGuard Home Power Users
The Problem: “Friction & Context Switching” Whether you run a single AdGuard Home instance on a Raspberry Pi or manage a fleet across multiple locations, the daily management experience often feels disconnected. To simply check if your server is online, pause protection for a quick test, or block an annoying tracker, you have to: It doesn’t seem like much, but
S3 Bucket Audit Report using AWS PowerShell Script – Secure your S3 Buckets
If you are working on AWS environment and if you follow the news related to AWS, you will probably know there are many major data breach happened because of the human negligence, where vast amount of data kept without any protection like encryption, public access blocking. It is all because of human error. We create S3 bucket, and start
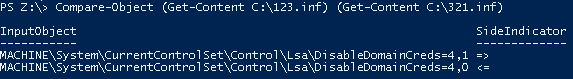
Task Scheduler Error “A specified logon session does not exist” – Fix via Command Line and PowerShell for Scripting
This is very know issue, if you search internet, you will get multiple blog post with same solution for this issue, and if you follow the steps, it actually resolve this issue. In simple word, solution of this problem is Logon to the faulty system. Open SECPOL.MSC from Run Go to Security Settings | Local Policies | Security Options Open
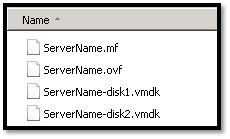
Migrating a VMWARE VM to AWS using AWS PowerShell
In this topic we will describes the necessary steps to migrate a VMWare VM to the Amazon Web Services (AWS) using PowerShell. You could also migrate VM using AWS command line tools, but I found using PowerShell is much easier than command line tools. Requirements: AWS Tools for Windows PowerShell http://aws.amazon.com/powershell/ IAM account to authenticate. Basic knowledge on PowerShell. Preparing