
Microsoft’s Secure Boot certificates issued in 2011 are approaching their expiration window in 2026. While affected devices will continue to boot and receive regular Windows updates, they will stop receiving new protections for the pre-boot environment — updates to Windows Boot Manager, Secure Boot DB/DBX revocations, and mitigations for newly discovered boot-level vulnerabilities. Many newer PCs already include the 2023 certificates, but organizations should act now to inventory, monitor, pilot, and deploy certificate updates so all devices continue to receive full Secure Boot protections.
What expires and when
Microsoft has issued updated 2023 certificates to replace the original 2011 certificates. The most immediate expirations to plan for are in June 2026 (with one key certificate’s replacement stretching to October 2026). The table below summarizes the certificates, their purpose, and the replacement certificates.
| Expiring Certificate | Expiration date | New Certificate | Storing location | Purpose |
|---|---|---|---|---|
| Microsoft Corporation KEK CA 2011 | June 2026 | Microsoft Corporation KEK 2K CA 2023 | KEK | Signs updates to DB and DBX. |
| Microsoft Windows Production PCA 2011 | Oct 2026 | Windows UEFI CA 2023 | DB | Signs the Windows boot loader. |
| Microsoft UEFI CA 2011* | June 2026 | Microsoft UEFI CA 2023 | DB | Signs third-party boot loaders and EFI applications. |
| Microsoft UEFI CA 2011* | June 2026 | Microsoft Option ROM UEFI CA 2023 | DB | Signs third-party option ROMs |
*During renewal the UEFI CA was split so option ROM signing can be managed separately from boot‑loader signing.
Why this matters for IT teams
- Security coverage: Devices that never get the updated certificates can no longer receive future Secure Boot protections, leaving the early boot environment unprotected against newly discovered threats (for example mitigations related to CVE-2023-24932 / BlackLotus).
- Compatibility risk: Some devices will require OEM firmware updates so the new certificates are accepted by the platform firmware.
- Operational impact: Systems will continue to boot and can receive typical OS updates, but organizations that rely on Secure Boot for scenarios like BitLocker hardening or validated boot chains should ensure certificates are updated to retain those protections.
How Microsoft and OEMs are delivering updates
- Microsoft is delivering new Secure Boot certificates through Windows monthly updates to “high-confidence” devices by default. Many devices manufactured since 2024 already ship with the 2023 certificates.
- OEMs are publishing firmware (BIOS/UEFI) updates where necessary to ensure devices accept the new certificates.
- For devices that need controlled or customer-managed rollouts, Microsoft provides several deployment options and registry-based mechanisms, and has published guidance and tooling (including WinCS APIs) for IT professionals.
A practical step-by-step playbook
- Inventory and prepare your environment
- Identify which devices have Secure Boot enabled and which have the 2023 certificates. Use Windows Autopatch’s Secure Boot status report or sample PowerShell inventory commands.
- Check the UEFICA2023Status registry value to determine deployment state (not started, in progress, updated) and build a representative pilot group focused on lower-confidence or less-common hardware.
- Monitor current status
- Monitor UEFICA2023Status and UEFICA2023Error registry keys.
- Use Windows System Event Log: Event ID 1808 indicates a successful certificate application; Event ID 1801 flags that the updated certificates were not applied; Event ID 1795 may indicate a firmware handoff error.
- In Intune, use the Secure Boot status report or the Windows quality updates reports to track device certificate status.
- Apply OEM firmware updates where recommended
- If OEM guidance or your testing indicates compatibility issues, apply the latest BIOS/UEFI updates before deploying Secure Boot certificate updates. OEM firmware updates can include fixes or updated certificate stores required for the new certificates to be accepted.
- Plan and pilot certificate deployments
- Pilot any chosen deployment method on a representative set of devices. Allow roughly 48 hours and one or more restarts for changes to fully apply in a real-world deployment.
- Avoid mixing deployment methods on the same device.
- Deployment methods (options for IT)
- Microsoft Intune (recommended for many scenarios)
- Intune provides three Secure Boot-related settings: Enable SecureBoot Certificate Updates, Configure Microsoft Update Managed Opt In, and Configure High Confidence Opt-Out. These let you enable automatic deployment, opt into Microsoft-managed controlled rollouts, or opt out of Microsoft automatic updates.
- Registry keys
- For devices you manage directly, the AvailableUpdates registry key under HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecureBoot can be set (for example 0x5944 to deploy all needed certificates and update to the 2023 boot manager). Use the UEFICA2023Status and UEFICA2023Error keys to monitor progress and errors.
- WinCS (Windows Configuration System)
- New command-line tools and PowerShell modules are available for domain‑joined clients on supported Windows 11 releases to query and apply Secure Boot configurations locally. Example: Feature_AllKeysAndBootMgrByWinCS with the WinCS key value referenced in Microsoft guidance.
- Group Policy
- Group Policy exposes Enable Secure Boot certificate deployment and related settings. Ensure you have the latest Administrative Templates (.admx) for Windows so policy settings and descriptions are current.
- Microsoft Intune (recommended for many scenarios)
Common troubleshooting scenarios
- UEFICA2023Error exists: Consult Secure Boot DB and DBX variable update events for remediation steps. An error key with a nonzero value indicates a pending issue.
- AvailableUpdates stuck with a 0x0004 bit: If the device doesn’t progress past the Key Exchange Key (KEK) update (AvailableUpdates stuck at 0x4104), coordinate with the OEM to confirm their implementation of Secure Boot key handling follows Microsoft’s OEM guidance.
- Event ID 1795: Indicates an error handing off certificates to firmware — typically points to needing an OEM firmware update.
Recommended rollout plan
- Week 0–2: Inventory and classify devices by Secure Boot status and firmware age. Identify high-confidence devices that Microsoft will auto-update and low-confidence devices that need manual intervention.
- Week 2–6: Pilot on a small, representative set that includes older and less-common hardware. Validate firmware updates where indicated.
- Week 6–12: Broader phased deployment using Intune or chosen management approach. Monitor event logs and registry keys for issues and remediate per guidance.
- Ongoing: Keep devices up to date with firmware and OS updates, and monitor Secure Boot status reports in Intune/Autopatch.
Final checklist for IT teams
- Inventory Secure Boot enablement and UEFICA2023Status across fleet.
- Apply OEM firmware updates where recommended before certificate deployment.
- Choose and pilot one deployment method (Intune, registry, WinCS, or GPO) — do not mix methods on the same device.
- Monitor Windows Event Log (1808, 1801, 1795) and UEFICA2023Error for failures and work with OEMs when firmware issues appear.
- Document rollback and recovery steps for devices that do not accept the new certificates.
- Bookmark Microsoft’s central Secure Boot resource (aka.ms/GetSecureBoot) for updates and new tools.

The Credential-Free Watchdog: Mastering Event-Driven App Automation
We have all been there. You are an automation lover. You have…
Microsoft Teams’ Efficiency Mode Arrives for Low‑End Devices
Microsoft is rolling out an Efficiency Mode for Microsoft Teams designed to…
How Attackers Abuse Microsoft Teams and Quick Assist: Inside the Helpdesk Impersonation Playbook
A new wave of attacks is quietly abusing everyday collaboration tools to…
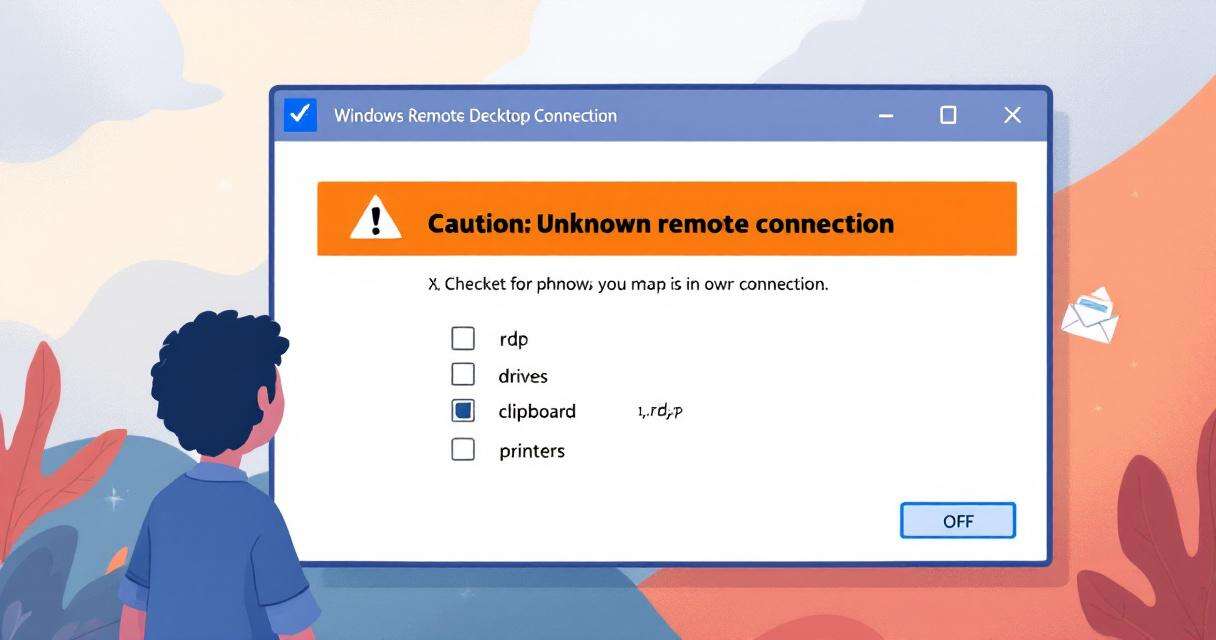
New RDP Alert After April 2026 Security Update Warns of Unknown Connections
Microsoft’s April 2026 Patch Tuesday introduced a small-looking but important change to…