
Phishing has evolved from crude scams to carefully engineered deceptions that mimic trusted internal processes. In mid‑April 2026, Microsoft Defender Research observed a large, multi‑stage campaign that did exactly that: it masqueraded as internal “code of conduct” notifications, used polished templates and legitimate delivery services, and funneled victims through a sequence of CAPTCHA and staging pages that ultimately proxied real authentication flows. The result was an adversary‑in‑the‑middle (AiTM) compromise capable of capturing authentication tokens and bypassing non‑phishing‑resistant multifactor authentication.
How the campaign posed as legitimate compliance notices
Attackers crafted emails that looked and read like internal compliance or regulatory communications. Display names such as “Internal Regulatory COC” and subject lines like “Internal case log issued under conduct policy” created a sense of internal urgency. Messages referenced organization‑specific details, included statements asserting that links and attachments had been “reviewed and approved for secure access,” and even added an encrypted‑message banner referencing Paubox to reinforce credibility for recipients who might associate that service with HIPAA‑compliant communications. Each message carried a PDF attachment with filenames implying formal case documentation, for example “Awareness Case Log File – Tuesday 14th, April 2026.pdf” and “Disciplinary Action – Employee Device Handling Case.pdf.” The PDFs directed recipients to click a “Review Case Materials” link that launched the attack chain.
Scope and targeting of the campaign
Between April 14 and 16, 2026, the campaign sent waves of messages that targeted over 35,000 users across more than 13,000 organizations in 26 countries, with roughly 92% of targets located in the United States. The campaign did not single out a single sector; it swept broadly but had the highest share of targets in Healthcare and life sciences (19%), Financial services (18%), Professional services (11%), and Technology software (11%). Messages arrived in distinct bursts over a roughly two‑day period, indicating coordinated distribution and a staged operational tempo.
Multi‑stage social engineering and delivery infrastructure
Rather than a single landing page, the campaign used a chain of pages and gating steps designed to filter automated analysis and to convince human targets of legitimacy.
- Legitimate‑appearing senders and delivery services: Analysis showed the campaign used a legitimate email delivery service and cloud infrastructure—likely a cloud‑hosted Windows VM—to send fully authenticated messages from attacker‑controlled domains and multiple sender addresses.
- PDF attachment as the initial hook: The attached PDFs provided context that resembled formal internal documentation and contained a link to the credential harvesting flow.
- CAPTCHA gating: Clicking the PDF link first led to attacker domains that presented a Cloudflare CAPTCHA. This likely served to slow or block automated crawlers and sandboxes.
- Intermediate legitimizing page: After the CAPTCHA, victims were sent to an intermediate page explaining the documentation was encrypted and required account authentication—an additional step to build trust and reduce suspicion.
- Additional CAPTCHA and image‑selection challenges: Before the final sign‑in prompt, victims sometimes faced a second image‑selection CAPTCHA, further reinforcing the idea of a secure, legitimate process and continuing to thwart automated detection.
- Device‑aware redirection: JavaScript on the final redirect stage routed users to different final pages depending on whether they visited from mobile or desktop, tailoring the phishing experience for the platform.
AiTM token capture through proxied Microsoft sign‑in
The final stage presented victims with a “Sign in with Microsoft” option that redirected to a Microsoft authentication page while simultaneously initiating an AiTM proxy flow. Rather than simply harvesting credentials entered into a fake form, the AiTM setup proxied the authentication session in real time to intercept authentication tokens. These tokens can grant immediate account access and sidestep traditional MFA protections that are not phishing resistant (for example, SMS or simple authenticator prompts). Because the flow worked through legitimate authentication redirects and looked like an official sign‑in, it substantially increased the risk of successful token compromise.
Why AiTM is more dangerous than credential harvesting
Classic credential harvesting relies on static capture of usernames and passwords submitted to fake forms. AiTM attacks go further by acting as a transparent intermediary during the legitimate authentication process. This allows attackers to intercept tokens, session cookies, or other artifacts that provide access without needing to know the user’s password, and they can evade defenses that only look for credential‑entry forms or reused passwords. Importantly, AiTM can defeat many MFA implementations because the attacker proxies the MFA challenge and response in real time.
Mitigations and recommended defenses
Microsoft’s analysis emphasizes layered defenses that combine user training, email protections, browser protections, authentication hardening, and automated attack disruption:
- Harden email controls: Review and apply recommended settings for Exchange Online Protection and Microsoft Defender for Office 365, including Safe Links and Safe Attachments, and enable Zero‑hour auto purge (ZAP) so newly discovered threats can be retroactively removed from mailboxes.
- Train users with realistic simulations: Invest in user awareness and phishing simulation programs. Use attack simulation training tools to expose users to multi‑step lures resembling this campaign.
- Use phishing‑resistant authentication: Deploy password‑less methods where possible (Windows Hello, FIDO keys, Microsoft Authenticator in password‑less mode) and use authenticator apps for MFA. Apply conditional access policies and require phishing‑resistant MFA for privileged or high‑risk accounts.
- Protect endpoints and networks: Enable network protection and encourage browsers that support Microsoft Defender SmartScreen to block known phishing domains and malicious pages. Configure Defender for Endpoint network protections to route suspicious web traffic through SmartScreen.
- Monitor and respond quickly: Use Threat Explorer and advanced hunting queries in Microsoft Defender XDR to find and purge similar phishing emails. Configure automatic attack disruption to limit the impact of an attack in progress and buy time for responders to remediate.
- Detection and telemetry: Correlate anomalous sign‑in behaviors, unfamiliar sign‑in properties, impossible travel activity, and detection signals across email, endpoint, and identity telemetry to detect abuse of compromised tokens.
Microsoft Defender coverage
Microsoft Defender coordinates detection and response across endpoints, email, identities, and cloud apps to help identify and contain campaigns like this one. The blog lists defender detections tied to campaign tactics and observed activity, including email detection signals and identity protections.
| Tactic | Observed activity | Microsoft Defender coverage |
|---|---|---|
| Initial access | Phishing emails | Microsoft Defender for Office 365 – A potentially malicious URL click was detected – A user clicked through to a potentially malicious URL – Suspicious email sending patterns detected – Email messages containing malicious URL removed after delivery – Email messages removed after delivery – Email reported by user as malware or phish |
| Persistence | Threat actors sign in with stolen valid entities | Microsoft Entra ID Protection – Anomalous Token – Unfamiliar sign-in properties – Unfamiliar sign-in properties for session cookies Microsoft Defender for Cloud Apps – Impossible travel activity |
Operational takeaways for defenders
– Treat unexpected “internal” compliance notices with suspicion, especially when they require immediate action or ask you to open attachments and follow external links.
– Combine technical controls with user training: automated protections reduce exposure at scale, and training reduces the chance an individual will engage with a sophisticated lure.
– Prioritize phishing‑resistant authentication and conditional access for high‑value accounts to limit the effectiveness of AiTM techniques.
– Maintain cross‑signal hunting and response playbooks that tie email detections to identity and endpoint telemetry so teams can quickly identify compromised sessions and revoke tokens.
This campaign illustrates how attackers blend social engineering, legitimate infrastructure, and multi‑step gating to outpace simple detection rules. Defenders must respond in kind: improve email hygiene, employ stronger authentication, and use integrated telemetry and automation to detect and stop adversaries that try to break the code of trust inside organizations.

Hackers Leverage Microsoft Teams to Breach Organizations: Inside UNC6692’s SNOW Campaign
In late 2025 and into early 2026, a sophisticated intrusion campaign used…
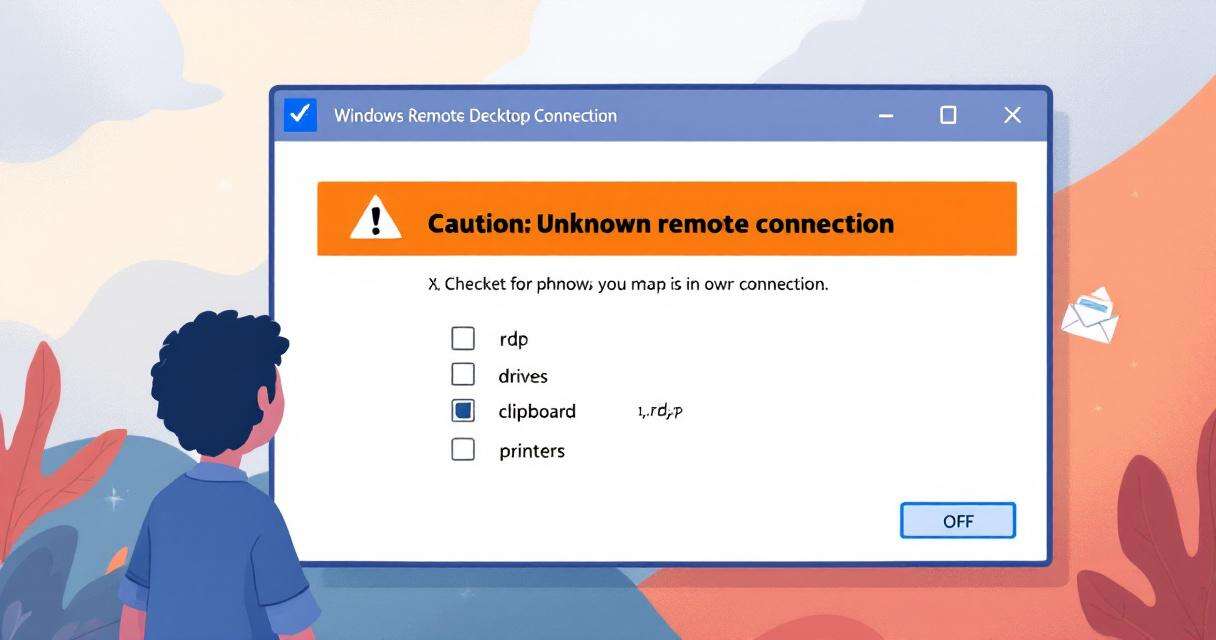
New RDP Alert After April 2026 Security Update Warns of Unknown Connections
Microsoft’s April 2026 Patch Tuesday introduced a small-looking but important change to…

Recently Leaked Windows Zero-Days Now Being Actively Exploited: What You Need to Know
Threat actors have begun abusing three recently disclosed Windows vulnerabilities to escalate…

RedSun: New Microsoft Defender Zero-Day Lets Unprivileged Users Gain SYSTEM Access
A freshly disclosed zero-day vulnerability in Microsoft Defender, dubbed "RedSun," has raised…