In early March 2026, Microsoft released an important security update addressing a high-severity vulnerability in Active Directory Domain Services (AD DS) tracked as CVE-2026-25177. The flaw received a CVSS score of 8.8 and can allow an authenticated network actor with limited permissions to escalate privileges to full SYSTEM on a targeted domain controller. Microsoft and third-party researchers coordinated fixes and
Category: Server and Virtualisation
Server Administration, Windows Server administration, Nginx, Apache, MySQL, PostgreSQL, MariaDB, MongoDB, VMware, vCenter, ESXi, Proxmox VE, Hyper-V, KVM, QEMU, libvirt, container, server monitoring, server security, SSH, remote access, FTP, SFTP, server performance, server hardening, iSCSI, NFS, SMB, CIFS, DNS server, DHCP server, web server, bare metal, rack server, IPMI, BIOS, RAID
Introducing the Azure Skills Plugin: Practical Azure Workflows for Coding Agents
The Azure Skills Plugin brings curated Azure expertise and an execution layer together so coding agents can do more than offer generic guidance. Rather than just suggesting commands or linking to documentation, the plugin packages decision logic (skills) and structured tools (MCP servers) so agents can reason about workflows and, when appropriate, run actions against real Azure resources. What the
Zero-Day on the Market: $220K Exploit Targets Windows Remote Desktop Services (CVE-2026-21533)
Remote Desktop Services (RDS) has come under renewed scrutiny after reports that a working exploit for CVE-2026-21533 — an elevation-of-privilege vulnerability in Windows Remote Desktop Services — was listed for sale on a dark web forum for $220,000. The listing and surrounding reporting are factual and straightforward: a recently created account advertised a claimed zero-day exploit, observers recorded the posting,
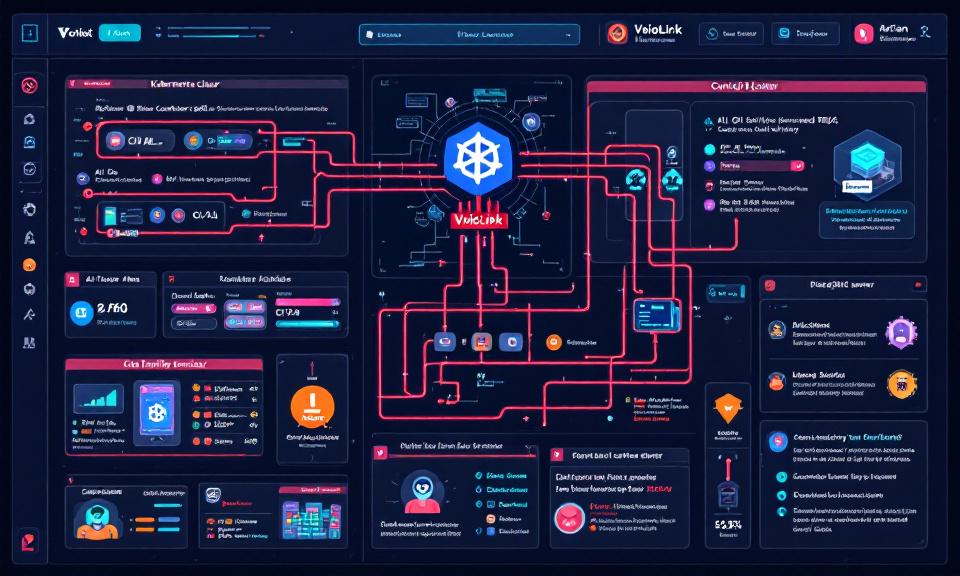
VoidLink Malware Framework: Key Points on How It Targets Kubernetes and AI Workloads
Title: VoidLink Malware Framework: Key Points on How It Targets Kubernetes and AI Workloads Overview VoidLink is a modular malware framework observed targeting cloud-native environments, with emphasis on Kubernetes clusters and AI infrastructure. Goal: persistence, lateral movement, data exfiltration, and abuse of compute (e.g., model theft, crypto-mining, or training/serving misuse). Modularity enables plugins for container escape, kubeconfig harvesting, and targeted
Enhanced Storage Resiliency with Azure NetApp Files Elastic Zone‑Redundant Service
Data resiliency is a baseline requirement for modern enterprise applications. Short interruptions or data loss can cascade into regulatory, financial, and reputational consequences. Azure NetApp Files (ANF) Elastic zone‑redundant storage (ANF Elastic ZRS) is a managed, multi‑AZ file storage option built on Azure’s ZRS architecture that aims to deliver synchronous multi‑zone replication, automatic failover, and enterprise ONTAP data management features
When an Upgrade Breaks the Network: Windows 11 23H2→25H2 and the 802.1X Policy Wipe
A quietly persistent bug in in-place Windows upgrades has resurfaced across recent Windows 11 version jumps and is creating a painful, real-world problem for enterprise IT teams: wired 802.1X authentication profiles applied by Group Policy are being deleted during some upgrades, leaving machines offline until a manual recovery is performed. What looks like a routine OS update can turn into