
For years, the internet’s move to post‑quantum cryptography focused first on TLS, but site‑to‑site networking has lagged behind. Today Cloudflare is announcing general availability of post‑quantum encryption for Cloudflare IPsec, bringing hybrid ML‑KEM protection to WAN tunnels so organizations can defend against “harvest‑now, decrypt‑later” attacks without buying specialized hardware. This update moves another critical piece of enterprise networking closer to a quantum‑resistant future as Cloudflare continues its push toward full post‑quantum security by 2029.
Cloudflare IPsec
Cloudflare IPsec is a managed WAN Network‑as‑a‑Service that replaces traditional site‑to‑site VPN appliances by connecting data centers, branch offices, and cloud VPCs into Cloudflare’s global anycast network. Customers gain simplified configuration, automatic failover across Cloudflare’s distributed edge, and the ability to secure traffic for site‑to‑site WAN, outbound internet connections, and integration with Cloudflare One SASE features. The recent update adds a post‑quantum option to these existing encrypted IPsec tunnels.
How hybrid ML‑KEM protects your tunnels
The new IPsec option uses a hybrid ML‑KEM key exchange (per the draft IETF spec draft‑ietf‑ipsecme‑ikev2‑mlkem) that combines classical Diffie‑Hellman with a module‑lattice‑based KEM. In practice a classical Diffie‑Hellman exchange runs first; the derived secret then encrypts a second exchange using ML‑KEM, and the outputs from both are mixed into the session keys that protect Encapsulating Security Payload (ESP) traffic. Because the scheme mixes classical and post‑quantum components, it preserves compatibility with existing cryptographic expectations while adding resistance to quantum adversaries that may appear in the future.
Why this matters: defending against harvest‑now, decrypt‑later
A main driver for post‑quantum adoption is the risk that adversaries could record today’s encrypted traffic and decrypt it later once large‑scale quantum computers exist. ML‑KEM is designed to be implemented in software on standard processors, avoiding the need for dedicated hardware or point‑to‑point quantum links. That makes it practical for Internet‑scale deployments and helps organizations reduce the window of vulnerability for sensitive communications.
Interoperability with existing hardware
Cloudflare’s implementation of the hybrid IPsec handshake has been tested and deployed broadly: it interoperates with reference implementations such as strongSwan and has been verified with branch connectors from major vendors. Cisco 8000 Series Secure Routers (from version 26.1.1) and Fortinet FortiOS (7.6.6 and later) can establish post‑quantum IPsec tunnels to Cloudflare’s network under the hybrid ML‑KEM draft. That interoperability is important because upgrading cryptography across distributed networks is operationally difficult; being able to reuse existing on‑premises hardware reduces friction for customers.
Standards, fragmentation, and why consensus matters
One reason post‑quantum support in IPsec lagged behind TLS is the pace of standardization and the presence of competing approaches. The IPsec community also explored Quantum Key Distribution (QKD) earlier, but QKD requires specialized physical links and hardware and does not provide authentication, limiting its practicality at Internet scale. RFC 9370 (2023) allowed multiple parallel key exchanges in IKEv2 but didn’t mandate which post‑quantum ciphers to use, leading some vendors to ship incompatible or non‑standard ciphersuites. The arrival of draft‑ietf‑ipsecme‑ikev2‑mlkem fills that gap by specifying a hybrid ML‑KEM approach that promotes interoperability and reduces the risk of “ciphersuite bloat.”
Remaining work: post‑quantum authentication and broader ecosystem alignment
While hybrid ML‑KEM addresses key exchange confidentiality, the standards landscape still needs consensus on post‑quantum authentication mechanisms for IPsec to ensure end‑to‑end protection against active quantum adversaries after Q‑Day. Continued coordination across vendors and adherence to interoperable IETF drafts will be critical to reach Cloudflare’s target of full post‑quantum readiness by 2029.
What customers should know now
Customers who rely on Cloudflare IPsec can enable post‑quantum hybrid ML‑KEM today to mitigate the risk of future decryption of captured traffic, and do so using many existing branch devices from major vendors. This capability is provided without requiring special hardware, and it aligns with Cloudflare’s broader work to make post‑quantum security practical and accessible at Internet scale.
Looking forward
Adopting post‑quantum cryptography across networking infrastructure is a multi‑year effort that hinges on interoperable standards and practical implementations. Cloudflare’s general availability for post‑quantum IPsec is a concrete step in that direction: it demonstrates an interoperable path for protecting WAN traffic today while the industry finishes work on authentication standards and continues to consolidate on scalable approaches.

Agents, Stripe Projects, and zero-friction Cloudflare provisioning
Agents can now take a project from idea to live production on…
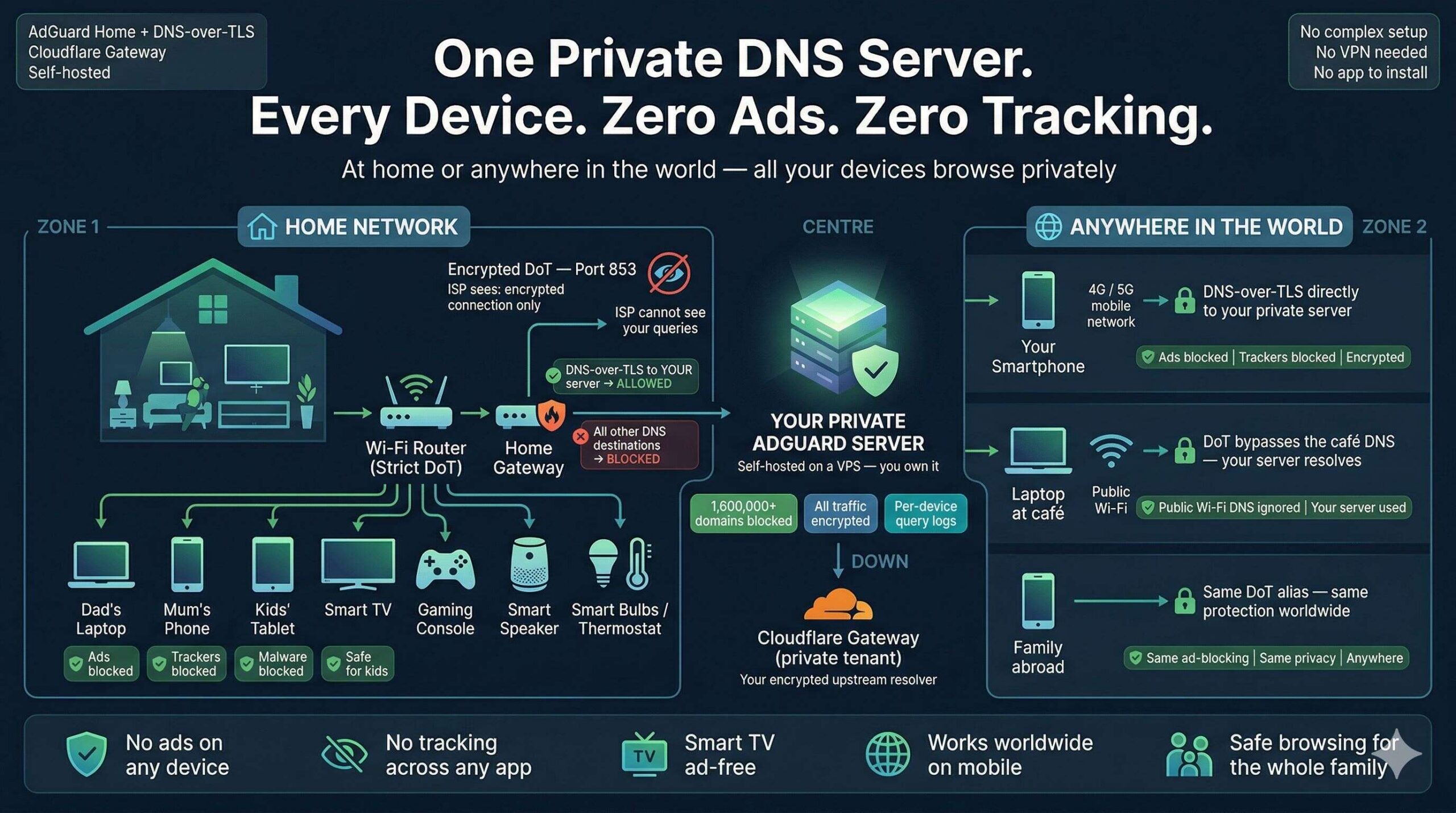
Zero Ads, Zero Tracking, Zero Exceptions: Build a Zero-Trust DNS Fortress for Every Device You Own
One self-hosted DNS server. Every device protected — at home and anywhere…

Face-Off: Windows PowerShell vs PowerShell Core — The Real-World Transition
PowerShell has come a long way since its inception, becoming an essential…
The Ultimate Command Center for AdGuard Home Power Users
The Problem: "Friction & Context Switching" Whether you run a single AdGuard…