
Microsoft’s April 2026 Patch Tuesday delivers a heavy set of fixes: 168 vulnerabilities across Windows, Office, Azure components and developer tools. The release includes one confirmed actively exploited zero-day in SharePoint Server (CVE-2026-32201) and a publicly disclosed elevation-of-privilege flaw in Microsoft Defender (CVE-2026-33825). Beyond those high-visibility issues, eight vulnerabilities are rated Critical — most of them Remote Code Execution (RCE) flaws — and dozens more allow elevation of privilege, information disclosure or denial-of-service conditions. For security teams, this month’s guidance is straightforward: prioritize the actively exploited SharePoint fix, treat the publicly disclosed Defender issue as urgent, and deploy the Critical RCE patches across affected systems without delay.
What was patched this month
Microsoft’s patch set spans a wide array of components: Windows kernel subsystems, networking stacks (TCP/IP, UPnP), Active Directory, Print Spooler and LSASS, Remote Desktop components, Office applications (Word, Excel, PowerPoint), .NET Framework and Visual Studio, Azure agents and Logic Apps, SQL Server, Hyper-V, Windows services such as Function Discovery and Desktop Window Manager, and several user-facing tools like Snipping Tool. The Windows UPnP Device Host and networking subsystems saw concentrated hardening, while document-related engines (Office suite) again accounted for multiple RCE and information-disclosure fixes.
Key high-risk vulnerabilities
- CVE-2026-32201 (SharePoint Server) — Spoofing vulnerability that Microsoft has confirmed is being actively exploited in the wild. Organizations using SharePoint should treat this as an emergency remediation.
- CVE-2026-33825 (Microsoft Defender) — An elevation-of-privilege flaw that was publicly disclosed prior to the patch release. Public disclosure increases the likelihood of exploitation; patch promptly.
- Critical-rated Remote Code Execution flaws — Eight Critical CVEs this month, most enabling remote code execution across core Windows services and protocols. Notable Critical RCEs include Windows TCP/IP (CVE-2026-33827), Active Directory (CVE-2026-33826), and Remote Desktop Client (CVE-2026-32157).
Impact breakdown
| Impact | Count |
|---|---|
| Elevation of Privilege | 93 |
| Information Disclosure | 21 |
| Remote Code Execution | 20 |
| Security Feature Bypass | 13 |
| Denial of Service | 10 |
| Spoofing | 8 |
| Tampering | 2 |
| Defense in Depth | 1 |
| Total | 168 |
Notable CVEs (selection)
| CVE | Impact | Description |
|---|---|---|
| CVE-2026-33829 | Spoofing | Windows Snipping Tool |
| CVE-2026-33827 | Remote Code Execution | Windows TCP/IP |
| CVE-2026-33826 | Remote Code Execution | Windows Active Directory |
| CVE-2026-33825 | Elevation of Privilege | Microsoft Defender |
| CVE-2026-33824 | Remote Code Execution | Windows IKE Extension |
| CVE-2026-33822 | Information Disclosure | Microsoft Office Word |
| CVE-2026-33120 | Remote Code Execution | SQL Server |
| CVE-2026-33116 | Denial of Service | .NET, .NET Framework, Visual Studio |
| CVE-2026-33115 | Remote Code Execution | Microsoft Office Word |
| CVE-2026-33114 | Remote Code Execution | Microsoft Office Word |
| CVE-2026-33104 | Elevation of Privilege | Windows Win32K – GRFX |
| CVE-2026-33103 | Information Disclosure | Microsoft Dynamics 365 (on-premises) |
| CVE-2026-33101 | Elevation of Privilege | Windows Print Spooler Components |
| CVE-2026-33100 | Elevation of Privilege | Windows Ancillary Function Driver for WinSock |
| CVE-2026-33099 | Elevation of Privilege | Windows Ancillary Function Driver for WinSock |
| CVE-2026-33098 | Elevation of Privilege | Windows Container Isolation FS Filter Driver |
| CVE-2026-33096 | Denial of Service | Windows HTTP.sys |
| CVE-2026-33095 | Remote Code Execution | Microsoft Office Word |
| CVE-2026-32226 | Denial of Service | .NET Framework |
| CVE-2026-32225 | Security Feature Bypass | Windows Shell |
| CVE-2026-32224 | Elevation of Privilege | Windows Server Update Service |
| CVE-2026-32223 | Elevation of Privilege | Windows USB Print Driver |
| CVE-2026-32222 | Elevation of Privilege | Windows Win32K – ICOMP |
| CVE-2026-32221 | Remote Code Execution | Microsoft Graphics Component |
| CVE-2026-32220 | Security Feature Bypass | Windows Virtualization-Based Security (VBS) Enclave |
| CVE-2026-32219 | Elevation of Privilege | Microsoft Brokering File System |
| CVE-2026-32218 | Information Disclosure | Windows Kernel |
| CVE-2026-32217 | Information Disclosure | Windows Kernel |
| CVE-2026-32216 | Denial of Service | Windows Redirected Drive Buffering |
| CVE-2026-32215 | Information Disclosure | Windows Kernel |
| CVE-2026-32214 | Information Disclosure | Universal Plug and Play (upnp.dll) |
| CVE-2026-32212 | Information Disclosure | Universal Plug and Play (upnp.dll) |
| CVE-2026-32203 | Denial of Service | .NET and Visual Studio |
| CVE-2026-32202 | Spoofing | Windows Shell |
| CVE-2026-32201 | Spoofing | Microsoft Office SharePoint |
| CVE-2026-32200 | Remote Code Execution | Microsoft Office PowerPoint |
| CVE-2026-32199 | Remote Code Execution | Microsoft Office Excel |
| CVE-2026-32198 | Remote Code Execution | Microsoft Office Excel |
| CVE-2026-32197 | Remote Code Execution | Microsoft Office Excel |
| CVE-2026-32196 | Spoofing | Windows Admin Center |
| CVE-2026-32195 | Elevation of Privilege | Windows Kernel |
| CVE-2026-32192 | Elevation of Privilege | Azure Monitor Agent |
| CVE-2026-32190 | Remote Code Execution | Microsoft Office |
| CVE-2026-32189 | Remote Code Execution | Microsoft Office Excel |
| CVE-2026-32188 | Information Disclosure | Microsoft Office Excel |
| CVE-2026-32187 | Defense in Depth | Microsoft Edge (Chromium-based) |
| CVE-2026-32184 | Elevation of Privilege | Microsoft High Performance Compute Pack (HPC) |
| CVE-2026-32183 | Remote Code Execution | Windows Snipping Tool |
| CVE-2026-32181 | Denial of Service | Microsoft Windows |
| CVE-2026-32178 | Spoofing | .NET |
| CVE-2026-32176 | Elevation of Privilege | SQL Server |
| CVE-2026-32171 | Elevation of Privilege | Azure Logic Apps |
| CVE-2026-32168 | Elevation of Privilege | Azure Monitor Agent |
| CVE-2026-32167 | Elevation of Privilege | SQL Server |
| CVE-2026-32165 | Elevation of Privilege | Windows User Interface Core |
| CVE-2026-32164 | Elevation of Privilege | Windows User Interface Core |
| CVE-2026-32163 | Elevation of Privilege | Windows User Interface Core |
| CVE-2026-32162 | Elevation of Privilege | Windows COM |
| CVE-2026-32160 | Elevation of Privilege | Windows Push Notifications |
| CVE-2026-32159 | Elevation of Privilege | Windows Push Notifications |
| CVE-2026-32158 | Elevation of Privilege | Windows Push Notifications |
| CVE-2026-32157 | Remote Code Execution | Remote Desktop Client |
| CVE-2026-32156 | Remote Code Execution | Windows Universal Plug and Play (UPnP) Device Host |
| CVE-2026-32155 | Elevation of Privilege | Desktop Window Manager |
| CVE-2026-32154 | Elevation of Privilege | Desktop Window Manager |
| CVE-2026-32153 | Elevation of Privilege | Microsoft Windows Speech |
| CVE-2026-32152 | Elevation of Privilege | Desktop Window Manager |
| CVE-2026-32151 | Information Disclosure | Windows Shell |
| CVE-2026-32150 | Elevation of Privilege | Function Discovery Service (fdwsd.dll) |
| CVE-2026-32149 | Remote Code Execution | Role: Windows Hyper-V |
| CVE-2026-32093 | Elevation of Privilege | Function Discovery Service (fdwsd.dll) |
| CVE-2026-32091 | Elevation of Privilege | Microsoft Brokering File System |
| CVE-2026-32090 | Elevation of Privilege | Windows Speech Brokered Api |
| CVE-2026-32089 | Elevation of Privilege | Windows Speech Brokered Api |
| CVE-2026-32088 | Security Feature Bypass | Windows Biometric Service |
| CVE-2026-32087 | Elevation of Privilege | Function Discovery Service (fdwsd.dll) |
| CVE-2026-32086 | Elevation of Privilege | Function Discovery Service (fdwsd.dll) |
| CVE-2026-32085 | Information Disclosure | Windows Remote Procedure Call |
| CVE-2026-32084 | Information Disclosure | Windows File Explorer |
| CVE-2026-32083 | Elevation of Privilege | Windows SSDP Service |
| CVE-2026-32082 | Elevation of Privilege | Windows SSDP Service |
| CVE-2026-32081 | Information Disclosure | Windows File Explorer |
| CVE-2026-32080 | Elevation of Privilege | Windows WalletService |
| CVE-2026-32079 | Information Disclosure | Windows File Explorer |
| CVE-2026-32078 | Elevation of Privilege | Windows Projected File System |
| CVE-2026-32077 | Elevation of Privilege | Windows Universal Plug and Play (UPnP) Device Host |
| CVE-2026-32076 | Elevation of Privilege | Windows Storage Spaces Controller |
| CVE-2026-32075 | Elevation of Privilege | Windows Universal Plug and Play (UPnP) Device Host |
| CVE-2026-32074 | Elevation of Privilege | Windows Projected File System |
| CVE-2026-32073 | Elevation of Privilege | Windows Ancillary Function Driver for WinSock |
| CVE-2026-32072 | Spoofing | Windows Active Directory |
| CVE-2026-32071 | Denial of Service | Windows Local Security Authority Subsystem Service (LSASS) |
| CVE-2026-32070 | Elevation of Privilege | Windows Common Log File System Driver |
| CVE-2026-32069 | Elevation of Privilege | Windows Projected File System |
| CVE-2026-32068 | Elevation of Privilege | Windows SSDP Service |
| CVE-2026-27931 | Information Disclosure | Windows GDI |
| CVE-2026-27930 | Information Disclosure | Windows GDI |
| CVE-2026-27929 | Elevation of Privilege | Windows LUAFV |
| CVE-2026-27928 | Security Feature Bypass | Windows Hello |
| CVE-2026-27927 | Elevation of Privilege | Windows Projected File System |
| CVE-2026-27926 | Elevation of Privilege | Windows Cloud Files Mini Filter Driver |
| CVE-2026-27925 | Information Disclosure | Windows Universal Plug and Play (UPnP) Device Host |
| CVE-2026-27924 | Elevation of Privilege | Desktop Window Manager |
| CVE-2026-27923 | Elevation of Privilege | Desktop Window Manager |
| CVE-2026-27922 | Elevation of Privilege | Windows Ancillary Function Driver for WinSock |
| CVE-2026-27921 | Elevation of Privilege | Windows TCP/IP |
| CVE-2026-27920 | Elevation of Privilege | Windows Universal Plug and Play (UPnP) Device Host |
| CVE-2026-27919 | Elevation of Privilege | Windows Universal Plug and Play (UPnP) Device Host |
| CVE-2026-27918 | Elevation of Privilege | Windows Shell |
| CVE-2026-27917 | Elevation of Privilege | Windows WFP NDIS Lightweight Filter Driver (wfplwfs.sys) |
Recommended actions for security teams
- Immediate: Patch SharePoint servers for CVE-2026-32201. Treat as emergency remediation where SharePoint is Internet-facing or accessible to many users.
- Urgent: Apply the Defender patch for CVE-2026-33825 because of prior public disclosure.
- Critical: Deploy all Critical-rated RCE patches (Windows TCP/IP, Active Directory, Remote Desktop Client, Office RCEs). RCE bugs at the network or service layer can lead to wormable outcomes in some environments.
- Review and test: WSUS-related and BitLocker-affecting fixes (CVE-2026-32224, CVE-2026-27913) to ensure update delivery and disk encryption integrity are not undermined during remediation.
- Audit: Inventory exposed services (RDP, SharePoint, SQL Server, UPnP), ensure exposure is minimized, and enable compensating controls (network segmentation, least privilege, multi-factor authentication).
- Monitoring: Increase EDR/IDS/IPS monitoring for exploitation indicators tied to the patched CVEs and hunt for suspicious activity around SharePoint and Defender components.
What this means for organizations
April’s Patch Tuesday is a reminder that Microsoft’s broad platform footprint creates many potential attack surfaces. Organizations should prioritize fixes that are actively exploited or publicly disclosed, focus resources on Critical RCE patches that threaten remote compromise, and maintain robust patch testing and deployment pipelines to avoid gaps. Teams with exposed SharePoint, Active Directory, and Remote Desktop services should expedite remediation and bolster monitoring while updates are applied.
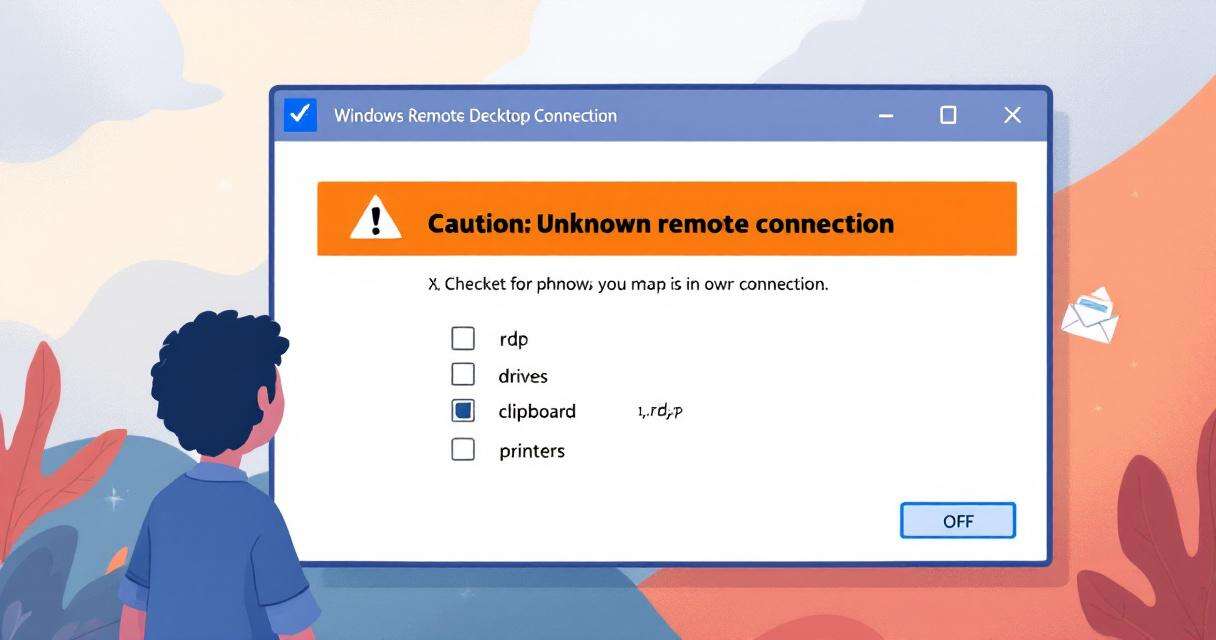
New RDP Alert After April 2026 Security Update Warns of Unknown Connections
Microsoft’s April 2026 Patch Tuesday introduced a small-looking but important change to…

RedSun: New Microsoft Defender Zero-Day Lets Unprivileged Users Gain SYSTEM Access
A freshly disclosed zero-day vulnerability in Microsoft Defender, dubbed "RedSun," has raised…

Breaking the code: how a multi-stage “code of conduct” phishing campaign led to AiTM token compromise
Phishing has evolved from crude scams to carefully engineered deceptions that mimic…
Critical Microsoft 365 Copilot Flaws: What Organizations Need to Know
Microsoft has disclosed and silently remediated three critical information-disclosure vulnerabilities in Microsoft…