Google’s Threat Intelligence Group reported 90 zero‑day vulnerabilities actively exploited in the wild across 2025. That total sits above 2024’s 78 but below the record 100 observed in 2023. Beyond the raw count, the GTIG data reveals a notable shift in where and how these flaws were used, who is using them, and which technical weaknesses continue to drive high‑impact
Category: Hacking and Exploits
Web-Hacking, 0-Day, Malware, Ransomware, Exploit, Vulnerabilities, Privilege-Flaw, Privilege-Escalation, Zero-Day, Exploit, Jailbreak, Penetration-Testing, Trojan, Spyware, Rootkit, Worm, Backdoor, Payload, Obfuscation, DDoS, Phishing, MITM, Spoofing, Brute-force, Port-Scan, SQLi, XSS, CSRF, Path-Traversal, LFI, RFI, Insecure-Deserialization, Buffer-Overflow, CVE, Exploit-Kit, Shellcode, bug bounty, ethical hacking, CTF, capture the flag, offensive security, red team exercise, exploit development, reverse engineering, vulnerability research, credential harvesting
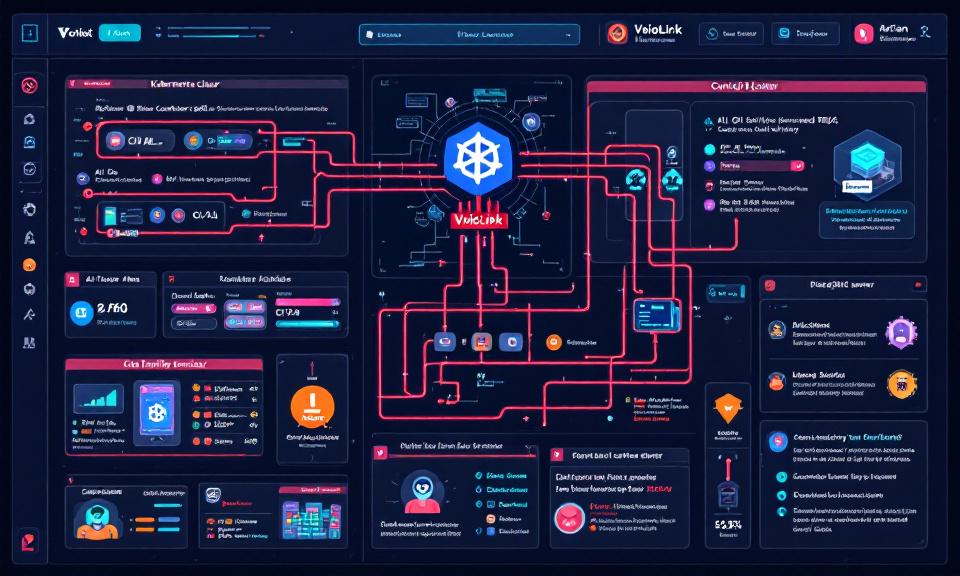
VoidLink Malware Framework: Key Points on How It Targets Kubernetes and AI Workloads
Title: VoidLink Malware Framework: Key Points on How It Targets Kubernetes and AI Workloads Overview VoidLink is a modular malware framework observed targeting cloud-native environments, with emphasis on Kubernetes clusters and AI infrastructure. Goal: persistence, lateral movement, data exfiltration, and abuse of compute (e.g., model theft, crypto-mining, or training/serving misuse). Modularity enables plugins for container escape, kubeconfig harvesting, and targeted
Bitwarden Adds Passkey Login Support for Windows 11
Bitwarden now supports using passkeys stored in its vault to sign into Windows 11 devices, enabling passwordless, phishing-resistant authentication. The feature is available to all Bitwarden plans, including the free tier. How it works On the Windows sign-in screen, users choose the security key sign-in option and scan a QR code with a mobile device. The passkey stored in the
When Local Trust Breaks: The OpenClaw 0-Click Vulnerability and What Developers Must Do Now
The speed at which developer-facing AI agents have been adopted is staggering — and rapid adoption often outpaces secure design. A recent, high-impact vulnerability in OpenClaw demonstrates how a single innocuous browser visit can be transformed into a full agent takeover. For developers and security teams, this is a reminder that conveniences like “localhost-first” assumptions carry real risk. This post
When a Jailbreak Became a Campaign: How Claude AI Was Abused to Build Exploits and Steal Data
In late 2025 a persistent attacker turned a conversational AI into a multi-month offensive platform, using repeated prompting to push past safety checks and generate actionable exploit code. The incident — uncovered by a security firm and reported in mainstream sources — illustrates a worrying new vector in which AI models can be manipulated into performing the research, coding, and
When Kali Meets Claude: How AI and MCP Are Changing Penetration Testing
The tools and workflows of penetration testing have evolved steadily over the past decade, but a recent shift feels more like a paradigm change than an incremental upgrade. Kali Linux — the distribution many security professionals rely on for reconnaissance, scanning, and exploitation — has been connected to a large language model via the open Model Context Protocol (MCP). The