A freshly disclosed zero-day vulnerability in Microsoft Defender, dubbed “RedSun,” has raised alarms across enterprise security teams: an unprivileged user can escalate to full SYSTEM-level access on fully patched Windows systems. The flaw was detailed publicly in April 2026 by a researcher known as “Chaotic Eclipse” (also referenced as Nightmare‑Eclipse on GitHub). Independent verification from vulnerability analyst Will Dormann confirms
Category: Server and Virtualisation
Server Administration, Windows Server administration, Nginx, Apache, MySQL, PostgreSQL, MariaDB, MongoDB, VMware, vCenter, ESXi, Proxmox VE, Hyper-V, KVM, QEMU, libvirt, container, server monitoring, server security, SSH, remote access, FTP, SFTP, server performance, server hardening, iSCSI, NFS, SMB, CIFS, DNS server, DHCP server, web server, bare metal, rack server, IPMI, BIOS, RAID
One-Click RCE in Azure Windows Admin Center: what happened and what you need to do
Windows Admin Center (WAC) is a convenient, browser-based management hub for administrators to manage servers, clients, and clusters from a centralized interface. A recent Cymulate Research Labs disclosure describes a critical chain of flaws that let an attacker achieve unauthenticated, one-click remote code execution (RCE) against both Azure-integrated and on-premises WAC deployments. The exploit requires little user interaction—a maliciously crafted
Microsoft Confirms Reboot Loops on Windows Server 2025 After April Patch KB5082063
Microsoft has confirmed a critical stability problem affecting some Windows Server 2025 domain controllers following the April 2026 cumulative update (KB5082063). Administrators around the world reported domain controllers entering repeated reboot cycles after installing the update released on April 14, 2026, and Microsoft’s release notes were updated to acknowledge the issue and a related installation failure affecting a subset of
Windows Secure Boot: A practical playbook for certificates expiring in 2026
Microsoft’s Secure Boot certificates issued in 2011 are approaching their expiration window in 2026. While affected devices will continue to boot and receive regular Windows updates, they will stop receiving new protections for the pre-boot environment — updates to Windows Boot Manager, Secure Boot DB/DBX revocations, and mitigations for newly discovered boot-level vulnerabilities. Many newer PCs already include the 2023
OpenAI’s GPT-5.4-Cyber: a practical boost for defenders — and a new risk calculus
OpenAI has introduced GPT-5.4-Cyber, a purpose-built variant of GPT-5.4 tuned to assist vetted security professionals with tasks previously reserved for specialized analysts. Rather than a general consumer release, this model is designed to lower refusal rates for legitimate cybersecurity workflows: binary reverse engineering, vulnerability scanning, malware analysis and exploit research. The announcement frames the model as a defensive accelerant —
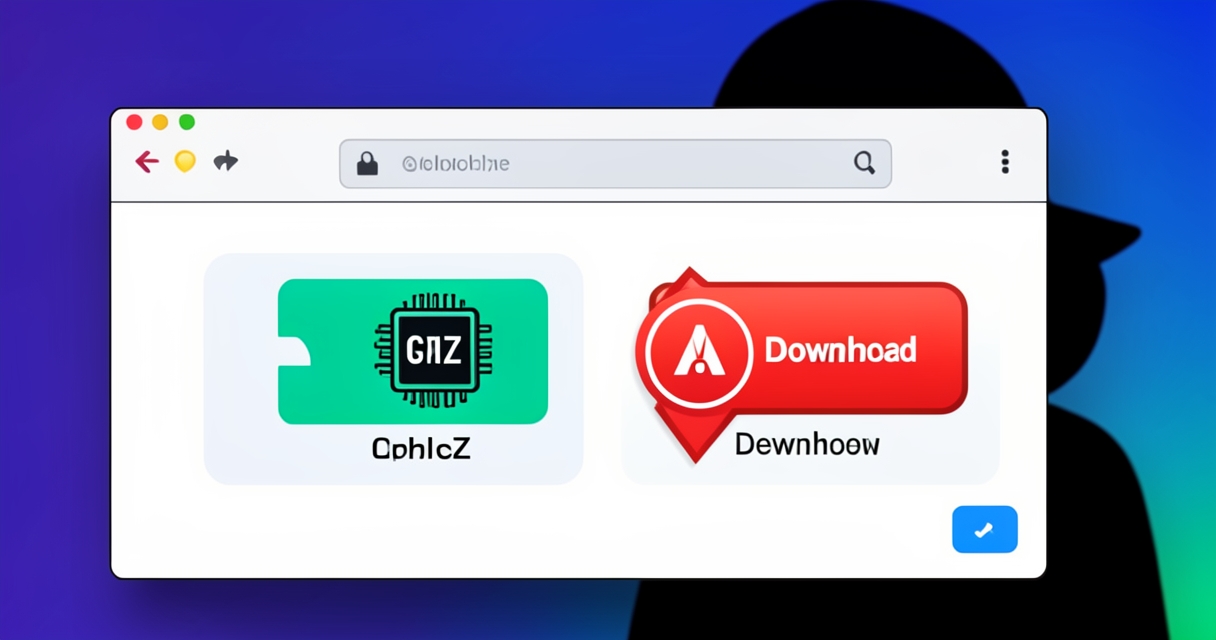
Compromised Trust: CPUID Supply‑Chain Attack Served Trojanized CPU‑Z and HWMonitor Installers
Hackers briefly hijacked a CPUID distribution channel and altered download links on the vendor’s official website so that users seeking the popular CPU‑Z and HWMonitor utilities would instead receive a trojanized installer. The modification redirected downloads to Cloudflare R2 storage and delivered a malicious file masquerading as HWiNFO, exposing millions of users who rely on these tools for hardware diagnostics