Target: Restrict creator / owner from altering any NTFS permission on newly created files & folders.
Scenarios: Regardless of NTFS permissions, the owner, which is by default the person who creates the folder/files, can always alter the permissions. This actually causing a lot’s of problem, with this special privilege users can also block inherited permission and alter current permission. This might cause additional pain for administrators.
Solution:
Initially to test this,
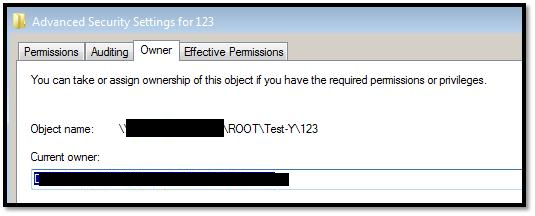
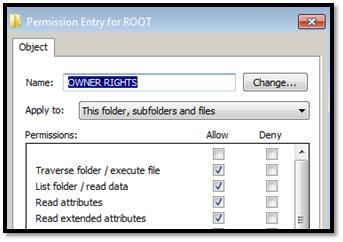
I have created one test folder \SHAREtestvolROOT without any inheritance and gave the Modify permission to XYZ group so that users can create folder. Additionally I gave Full access to Administrators group and READ, EXECUTE, LIST FOLDER permission to OWNER RIGHTS group on that folder with “Replace all Child object Permissions
” settings.
To evaluate the permission on \SHAREtestvolROOT, I asked users to create few folders, where they became owner by default.
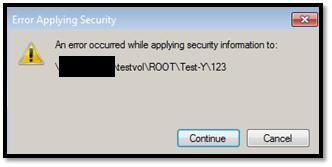
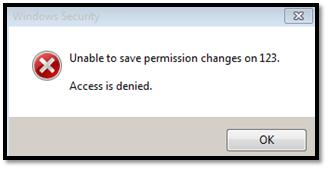
Then, I asked them to modify the permission on that folders, but they are getting access denied error, as we applied OWNER RIGHTS to prevent this.
So, with the current security settings using OWNER RIGHTS, now:
- Owner can create files & folders.
- Owner can modify files & folders.
- Owner can delete files & folder.
- Owner cannot modify any type of permission.
- Owner cannot block permission inheritance.
Ref: Owner Rights – http://technet.microsoft.com/en-us/library/dd125370%28v=ws.10%29.aspx

The Credential-Free Watchdog: Mastering Event-Driven App Automation
We have all been there. You are an automation lover. You have…
ClearView – Zero Configuration Web Server Monitoring Tool
Have you recently moved away from Linode to any other VPS (Virtual…

Create Private PPTP VPN for personal use in Linode Cloud Hosting.
Nowadays many things are getting blocked by the government, and sometimes without…
Add new Admin Account to AWS Windows Instances to rescue the system
As mentioned earlier, we could reset the local admin password of windows…
Really helpful article, very few knows about this granular permission
Great !!!!!
Really useful command and tested in production environment …it worked .
Finally… Thank you dude, it was really helpful !nn1