When Mike McClary decided to revive a discontinued flashlight that had once been one of his best sellers, he didn’t dust off the old supplier spreadsheet or spend weeks emailing factories. Instead, he opened Accio, an AI-powered sourcing assistant on Alibaba.com, and started a conversation. Within weeks he had a redesigned product, a recommended factory in Ningbo, and a projected
Category: Self Hosted
Nextcloud, Home Assistant, Plex, Jellyfin, Vaultwarden, Pi-hole, AdGuard Home, n8n, Proxmox, Portainer, TrueNAS, Grafana, Uptime Kuma, Syncthing, Gitea, WordPress, Ghost, Immich, Paperless-ngx, Mealie, Audiobookshelf, Homepage, Dashy, Heimdall, Authentik, Authelia, Traefik, Nginx Proxy Manager, WireGuard, Tailscale, BookStack, Navidrome, Kavita, Tandoor Recipes, Memos, Appsmith, Appwrite, Gogs, Seafile, PhotoPrism, Sonarr, Radarr, Lidarr, Prowlarr, Bazarr, Overseerr, OPNsense, pfSense, Stirling-PDF, OctoPrint, File Browser, homelab, self-hosting, home server, homelabbing
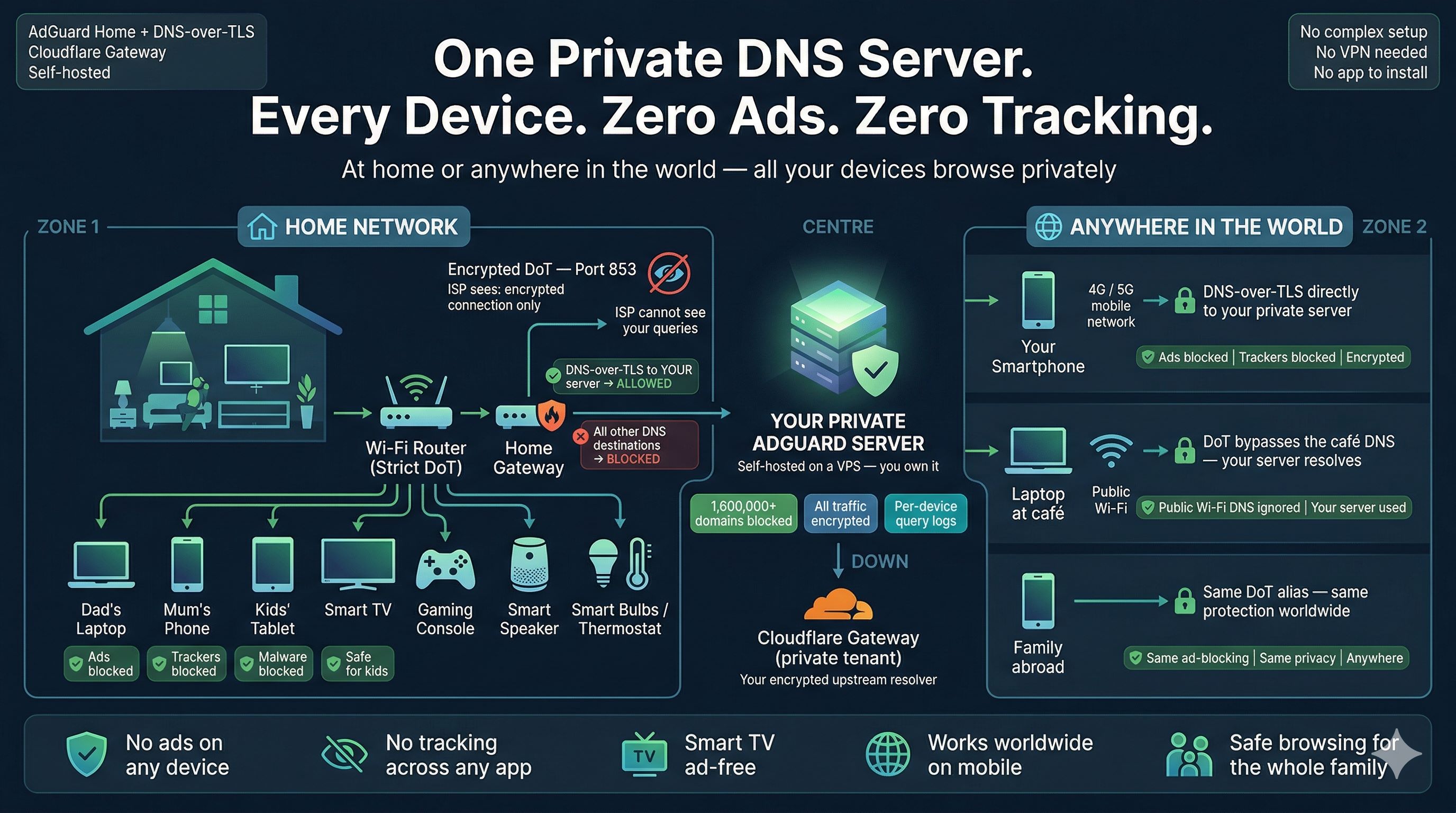
Zero Ads, Zero Tracking, Zero Exceptions: Build a Zero-Trust DNS Fortress for Every Device You Own
One self-hosted DNS server. Every device protected — at home and anywhere in the world. Here is a slightly terrifying, yet fun fact most people do not know: every time anyone in your household opens a browser, your Internet Service Provider (ISP) sees exactly which website they are visiting — before the page even loads. Not because they hacked your
Admin Account Backdoor: Critical Privilege-Flaw in WordPress User Registration Plugin (CVE-2026-1492)
A critical security flaw in a widely used WordPress membership plugin has made it trivially simple for unauthenticated attackers to create administrator accounts and seize control of affected sites. The vulnerability, tracked as CVE-2026-1492, exposes a systemic weakness in how the plugin handled role assignment during user registration. This post summarizes what happened, who discovered it, the immediate risks, and
From Tunnel to Cloud: The 2026 Strategy Guide to Self‑Hosting vs Third‑Party VPN
In 2026 the boundary between “VPN” and “personal cloud” is fuzzier than ever. A third‑party VPN still sells one‑click privacy and wide geo-hopping, but for many users that convenience now trades away transparency, extensibility, and long‑term value. Renting a small VPS and running WireGuard, AdGuard Home, Vaultwarden, and automation tools like n8n converts a disposable privacy tool into a persistent
Living with Smart Homes: How Connected Devices Are Reshaping Everyday Life
The concept of a “smart home” once sounded futuristic, but today, it’s quickly becoming part of ordinary life. A smart home ecosystem is more than just a collection of cool gadgets—it’s about seamlessly integrating devices to work together, make routines easier, and unlock conveniences that were hard to imagine just a decade ago. Whether you’re dimming the lights with a
Self-Hosted N8N on Affordable VPS: Practical Guide, Cost Comparisons, and Agentic AI Use Cases
Harnessing the power of self-hosted automation tools is transforming the way individuals and businesses streamline tasks. n8n (pronounced “n-eight-n”) is an open-source workflow automation tool known for its flexibility and the control it offers over data privacy and integrations. When paired with the capabilities of Agentic AI, it opens the door to advanced, intelligent workflows—without ever relying on expensive, proprietary