Security researchers recently uncovered a PowerShell script posted on Pastebin that was purpose-built to steal Telegram session data from both desktop and web clients. Masquerading as a benign “Windows Telemetry Update,” the script quietly collects host metadata, locates Telegram session stores, compresses them into an archive, and exfiltrates the file to an attacker-controlled Telegram bot. The discovery is notable less
Latest Articles

Palo Alto GlobalProtect CVE-2026-0257: Active Exploitation and Urgent Steps for Defenders
Palo Alto Networks has warned that a recently patched authentication bypass in PAN-OS GlobalProtect, tracked as CVE-2026-0257, is now being actively exploited in the wild. The vulnerability allows attackers to bypass authentication controls and establish unauthorized VPN connections when devices are configured with specific authentication override cookie and certificate settings. Organizations running GlobalProtect should treat this as urgent: apply vendor patches, review configurations, and hunt for signs of exploitation immediately. What the vulnerability is and why it matters CVE-2026-0257 is…
Continue readingDeepSeek V4: a cheaper, larger LLM that narrows the gap with frontier models
Chinese lab DeepSeek has released preview details for DeepSeek V4, a major update the company says brings its models much closer to so-called frontier systems. The announcement introduces two variants — V4 Flash and V4 Pro — and highlights big increases in scale, a 1 million-token context window, and aggressive pricing that positions the models as lower-cost alternatives to high-end
CISA: Zimbra XSS (CVE-2025-48700) Now Exploited — 10,500+ Servers Vulnerable
Over 10,000 instances of the Zimbra Collaboration Suite are exposed online and remain vulnerable to an actively exploited cross-site scripting flaw, raising fresh alarms about email server security for governments and businesses alike. The vulnerability, tracked as CVE-2025-48700, is serious because it can be triggered without user interaction and has been confirmed as abused in the wild, prompting action from
Hackers Leverage Microsoft Teams to Breach Organizations: Inside UNC6692’s SNOW Campaign
In late 2025 and into early 2026, a sophisticated intrusion campaign used the everyday familiarity of Microsoft Teams to turn routine collaboration into a direct route for enterprise compromise. By posing as IT helpdesk staff and exploiting users’ trust in external Teams invitations, the threat group tracked as UNC6692 moved from a simple chat message to full domain-level access—without exploiting
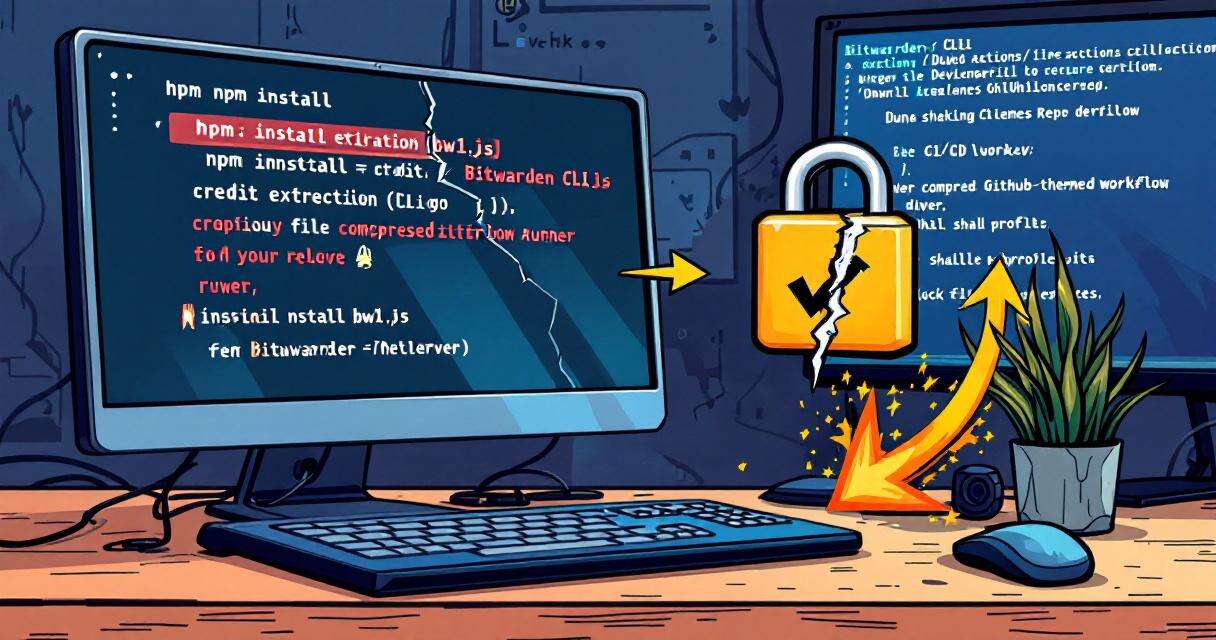
Bitwarden CLI Compromised in Supply Chain Attack via GitHub Actions
Socket and other researchers have confirmed that the Bitwarden CLI package published to npm — @bitwarden/cli version 2026.4.0 — was compromised in a supply chain attack that abused a GitHub Action in Bitwarden’s CI/CD pipeline. The malicious release injected a file named bw1.js into the package, exposing tokens, cloud credentials, SSH keys and other sensitive artifacts. While Bitwarden’s Chrome extension,
OpenAI Debuts Shared Workspace Agents to Automate Team Handoffs
OpenAI has introduced a new class of ChatGPT tools called shared workspace agents — always-on assistants designed to carry work across systems and through multi-step processes without constant human prompting. Built on Codex, these agents aim to reduce the friction of manual handoffs inside teams by gathering information from connected systems, executing defined steps, and returning results in a way