Amazon has quietly shifted the rules of engagement for its internal developer community. In a recent staff note, the company announced that tens of thousands of its developers will now have immediate access to Anthropic’s Claude Code and, soon, OpenAI’s Codex — both hosted on AWS and Amazon Bedrock. The move signals a notable loosening of earlier restrictions that favored
Latest Articles

Palo Alto GlobalProtect CVE-2026-0257: Active Exploitation and Urgent Steps for Defenders
Palo Alto Networks has warned that a recently patched authentication bypass in PAN-OS GlobalProtect, tracked as CVE-2026-0257, is now being actively exploited in the wild. The vulnerability allows attackers to bypass authentication controls and establish unauthorized VPN connections when devices are configured with specific authentication override cookie and certificate settings. Organizations running GlobalProtect should treat this as urgent: apply vendor patches, review configurations, and hunt for signs of exploitation immediately. What the vulnerability is and why it matters CVE-2026-0257 is…
Continue readingCritical Palo Alto Firewall Flaw: CVE-2026-0300 Exploited to Gain Root Access
Palo Alto Networks has disclosed a critical buffer overflow vulnerability in PAN-OS that is already being exploited in the wild. The flaw, tracked as CVE-2026-0300, can allow unauthenticated attackers to run arbitrary code with full root privileges on affected PA-Series and VM-Series firewalls when the User-ID™ Authentication Portal (captive portal) is exposed to untrusted networks. Given the ease of exploitation
Copy Fail (CVE-2026-31431): A 4‑Byte Kernel Bug That Lets Attackers Gain Root on Major Linux Distros
Microsoft Defender Security Research recently disclosed CVE-2026-31431—nicknamed “Copy Fail”—a high‑severity local privilege escalation in the Linux kernel’s crypto subsystem that enables an unprivileged user to escalate to root. The vulnerability affects kernels released since 2017 and has broad implications for cloud and container environments because the exploit can corrupt in-memory representations of readable files (including setuid binaries) without changing the
Amazon Faces Months of Repairs After Drone Strikes Cripple Middle East Data Centers
Amazon Web Services says recovery from drone strikes that hit its data centers in the United Arab Emirates and Bahrain will be measured in months, leaving customers in the region facing prolonged disruption and prompting a broader rethink of investments in Middle East infrastructure. The attacks, part of a wider bout of regional hostilities, knocked core compute racks offline, triggered
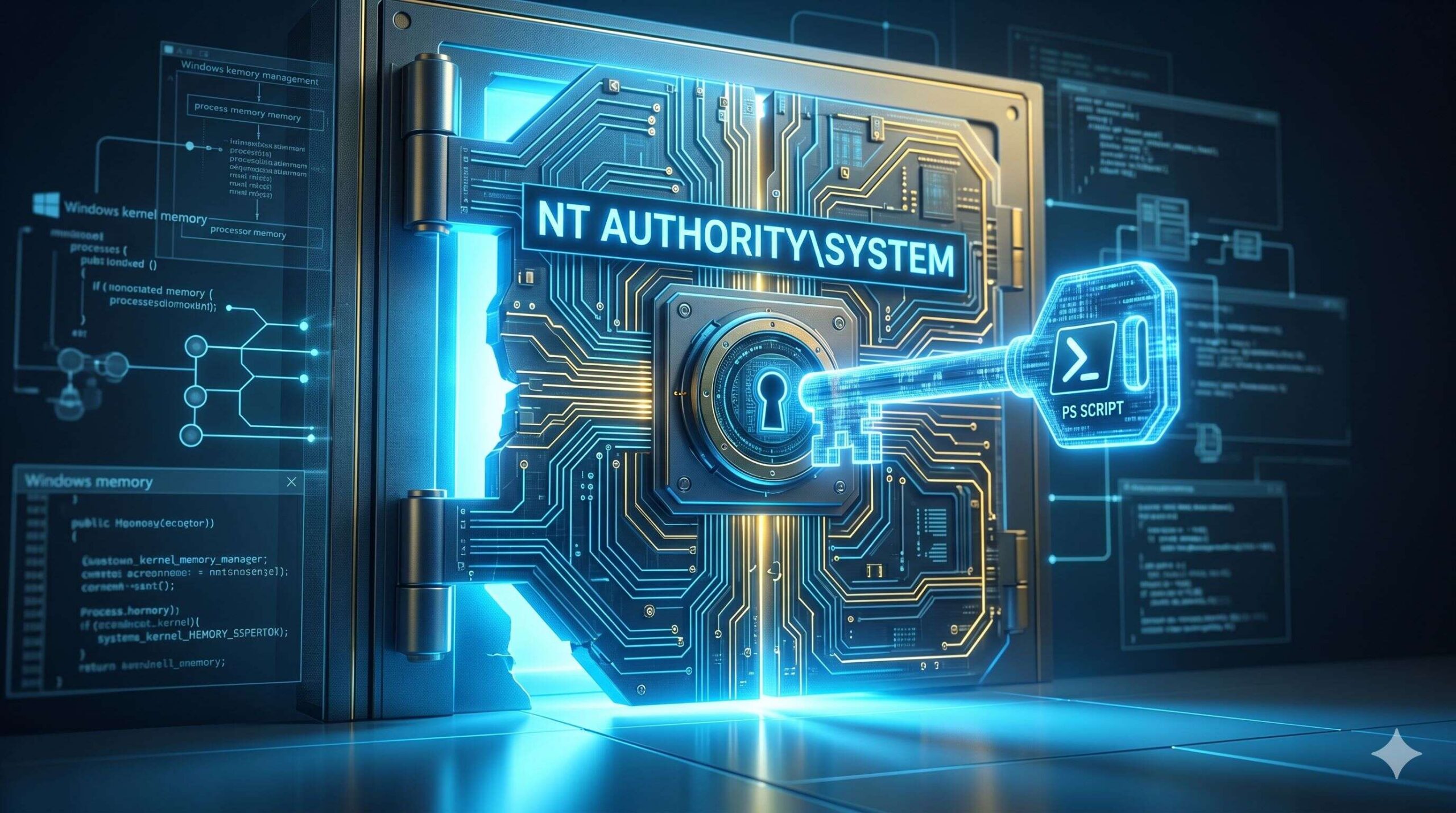
Ditching PsExec – Running Interactive SYSTEM Shells Natively in PowerShell
If you’ve spent any time in Windows System Administration over the last decade, I can almost guarantee you’ve reached for PsExec at least once. Originally from Sysinternals and now officially part of Microsoft, PsExec is one of those deceptively simple tools that has quietly saved thousands of IT professionals from hours of sheer agony. A single executable, zero installation, no
Cloudflare makes post‑quantum IPsec generally available
For years, the internet’s move to post‑quantum cryptography focused first on TLS, but site‑to‑site networking has lagged behind. Today Cloudflare is announcing general availability of post‑quantum encryption for Cloudflare IPsec, bringing hybrid ML‑KEM protection to WAN tunnels so organizations can defend against “harvest‑now, decrypt‑later” attacks without buying specialized hardware. This update moves another critical piece of enterprise networking closer to